The Null Device
Posts matching tags 'deception'
2014/1/20
A candidate for the most audacious bank heist in history happened in Japan in 1968, some time after a bank had started receiving bomb threats:
An armored car was making its way to deliver bonus payments for factory workers totaling nearly 300 million yen (roughly US$800,000, which accounting for inflation, is over $5 million in today’s dollars) when a policeman rode up on a motorcycle. The officer told the four bank employees on the truck that the manager’s house had just been blown up and that officials had received a warning that there was a bomb planted on the armored car they were driving. The officer then proceeded to look under the vehicle — and then came the smoke and flames.
The officer yelled for them to take cover, and they did, running toward the nearest building, which happened to be a prison. Once the four bank employees were at a safe distance from the apparently-about-to-explode car, the officer removed the threat from the area. He got behind the wheel of the armored car, still carrying all that money, and drove away.
He wasn’t a cop. And the dynamite under the car? Just a warning flare he set to flush the security detail out of the vehicle. The fake police officer had just pulled off the single largest heist in the history of Japan.The crime remains unsolved to this day.
2013/12/16
After it emerged that Thamsanqa Jantjie, the sign language interpreter at Nelson Mandela's memorial ceremony, had actually been making it up and just moving his arms about meaninglessly, Slavoj Žižek (no fan of well-meaning liberalism, to say the least) argues, with supreme cynicism, that his doing so was not so much a fraud as a deeper form of honesty, laying bare the hypocrisy of liberalism:
Now we can see why Jantjie's gesticulations generated such an uncanny effect once it became clear that they were meaningless: what he confronted us with was the truth about sign language translations for the deaf – it doesn't really matter if there are any deaf people among the public who need the translation; the translator is there to make us, who do not understand sign language, feel good.
And was this also not the truth about the whole of the Mandela memorial ceremony? All the crocodile tears of the dignitaries were a self-congratulatory exercise, and Jangtjie translated them into what they effectively were: nonsense. What the world leaders were celebrating was the successful postponement of the true crisis which will explode when poor, black South Africans effectively become a collective political agent. They were the Absent One to whom Jantjie was signalling, and his message was: the dignitaries really don't care about you. Through his fake translation, Jantjie rendered palpable the fake of the entire ceremonyOf course, actual deaf people might not agree with this assessment.
2013/7/10
An interesting article on cryptolects, secret group languages whose purpose is to conceal meaning from outsiders:
Incomprehension breeds fear. A secret language can be a threat: signifier has no need of signified in order to pack a punch. Hearing a conversation in a language we don’t speak, we wonder whether we’re being mocked. The klezmer-loshn spoken by Jewish musicians allowed them to talk about the families and wedding guests without being overheard. Germanía and Grypsera are prison languages designed to keep information from guards – the first in sixteenth-century Spain, the second in today’s Polish jails. The same logic shows how a secret language need not be the tongue of a minority or an oppressed group: given the right circumstances, even a national language can turn cryptolect. In 1680, as Moroccan troops besieged the short-lived British city of Tangier, Irish soldiers manning the walls resorted to speaking as Gaeilge, in Irish, for fear of being understood by English-born renegades in the Sultan’s armies. To this day, the Irish abroad use the same tactic in discussing what should go unheard, whether bargaining tactics or conversations about taxi-drivers’ haircuts. The same logic lay behind North African slave-masters’ insistence that their charges use the Lingua Franca (a pidgin based on Italian and Spanish and used by traders and slaves in the early modern Mediterranean) so that plots of escape or revolt would not go unheard. A Flemish captive, Emanuel d’Aranda, said that on one slave-galley alone, he heard ‘the Turkish, the Arabian, Lingua Franca, Spanish, French, Dutch, and English’. On his arrival at Algiers, his closest companion was an Icelander. In such a multilingual environment, the Lingua Franca didn’t just serve for giving orders, but as a means of restricting chatter and intrigue between slaves. If the key element of the secret language is that it obscures the understandings of outsiders, a national tongue can serve just as well as an argot.The article goes on to mention polari, which originated as a travelling entertainers' argot and ended up being a cryptolect used by gay men in 20th-century Britain, becoming largely obsolescent after homosexuality was decriminalised, surviving as a piece of period colour in artefacts like Morrissey's song Piccadilly Palare.
With its roots in Yiddish, cant, Romani, and Lingua Franca, Polari was a meeting-place for languages of those who were too often forced to hit the road; groups who, however chatty, tend to remain silent in traditional historical accounts. Today, the spirit of Polari might be said to live on in Pajubá (or Bajubá), a contact language used in Brazil’s LGBT community, which draws its vocabulary from West African languages – testimony to the hybrid, polyvocal processes through which a cryptolect finds voice.Of course, as the whole point of a cryptolect is to conceal meaning, as soon as some helpful soul compiles a crib sheet, they kill that particular version of the language as surely as a butterfly collector with a killing jar. (An example of this that has become a comedic trope is parents, politicians and other grown-ups trying to be hip to the groovy lingo of teenagers and falling flat.)
The work of the chronicler of cryptolect must always end in failure. These are languages which need to do more than keep up with current usage: they have to stay ahead of it, burning bridges where the vernacular has come too close; keeping their distance from the clear, the comprehensible. When Harman returned to the subject of pedlars’ French, his promises of understanding came with a new caveat: ‘as [the canting crew] have begun of late to devise some newe tearmes for certaine things: so will they in time alter this, and devise as evill or worse’. We can’t write working dictionaries of secret languages, any more than we can preserve a childhood or catch a star.Not all cryptolects belong to marginalised, disempowered or nefarious outsider groups (say, itinerant thieves, galley slaves, sexual minorities or minors under the totalitarian regime of parental authority); various technical jargons have something of the cryptolect about them where they avoid using laypersons' terminology in favour of synonymous terms specific to their subcultures. This could be argued to be a good thing, as confusion can occur when words have both technical and vernacular meanings (take for example the word “energy” as used by physicists and New Age mystics). Indeed, whether, say, International Art English is a cryptolect could come down to whether it serves to actually communicate to an in-group or just as a form of ritual display.
2013/1/2
An article about Apollo Robbins, virtuoso pickpocket. The self-taught Robbins does not practice his impressive skills for theft, but rather as a theatrical pickpocket, and has been recently working with cognitive science researchers investigating how human attention works, and how a masterful pickpocket or similar manipulator can exploit its properties:
He is probably best known for an encounter with Jimmy Carter’s Secret Service detail in 2001. While Carter was at dinner, Robbins struck up a conversation with several of his Secret Service men. Within a few minutes, he had emptied the agents’ pockets of pretty much everything but their guns. Robbins brandished a copy of Carter’s itinerary, and when an agent snatched it back he said, “You don’t have the authorization to see that!” When the agent felt for his badge, Robbins produced it and handed it back. Then he turned to the head of the detail and handed him his watch, his badge, and the keys to the Carter motorcade.
Robbins needs to get close to his victims without setting off alarm bells. “If I come at you head-on, like this,” he said, stepping forward, “I’m going to run into that bubble of your personal space very quickly, and that’s going to make you uncomfortable.” He took a step back. “So, what I do is I give you a point of focus, say a coin. Then I break eye contact by looking down, and I pivot around the point of focus, stepping forward in an arc, or a semicircle, till I’m in your space.” He demonstrated, winding up shoulder to shoulder with me, looking up at me sideways, his head cocked, all innocence. “See how I was able to close the gap?” he said. “I flew in under your radar and I have access to all your pockets.”
But physical technique, Robbins pointed out, is merely a tool. “It’s all about the choreography of people’s attention,” he said. “Attention is like water. It flows. It’s liquid. You create channels to divert it, and you hope that it flows the right way.”Robbins figured out his craft independently, though has since dealt with criminal and/or ex-criminal pickpockets, including a criminal virtuoso whom he tried, unsuccessfully, to recruit to a think-tank including pickpockets, card cheats and ex-cops; the article does go into the tradecraft and argot of the professional criminal pickpocket and the institutions of this trade (which, notwithstanding whilst it may be in decline in America, is alive and well elsewhere; by the way, did you know that the band School of Seven Bells is named after a pickpockets' academy in Colombia?)
Street pickpockets generally work in teams, known as whiz mobs or wire mobs. The “steer” chooses the victim, who is referred to generically as the “mark,” the “vic,” or the “chump,” but can also be categorized into various subspecies, among them “Mr. Bates” (businessman) and “pappy” (senior citizen). The “stall,” or “stick,” maneuvers the mark into position and holds him there, distracting his attention, perhaps by stumbling in his path, asking him for directions, or spilling something on him. The “shade” blocks the mark’s view of what’s about to happen, either with his body or with an object such as a newspaper. And the “tool” (also known as the “wire,” the “dip,” or the “mechanic”) lifts his wallet and hands it off to the “duke man,” who hustles away, leaving the rest of the mob clean. Robbins explained to me that, in practice, the process is more fluid—team members often play several positions—and that it unfolds less as a linear sequence of events than as what he calls a “synchronized convergence,” like a well-executed offensive play on the gridiron.
(via Boing Boing) ¶ 0
2012/2/27
Stage magician Teller explains some of the cognitive principles behind the magician's craft:
1. Exploit pattern recognition. I magically produce four silver dollars, one at a time, with the back of my hand toward you. Then I allow you to see the palm of my hand empty before a fifth coin appears. As Homo sapiens, you grasp the pattern, and take away the impression that I produced all five coins from a hand whose palm was empty.
2. Make the secret a lot more trouble than the trick seems worth. You will be fooled by a trick if it involves more time, money and practice than you (or any other sane onlooker) would be willing to invest. My partner, Penn, and I once produced 500 live cockroaches from a top hat on the desk of talk-show host David Letterman. To prepare this took weeks. We hired an entomologist who provided slow-moving, camera-friendly cockroaches (the kind from under your stove don’t hang around for close-ups) and taught us to pick the bugs up without screaming like preadolescent girls. Then we built a secret compartment out of foam-core (one of the few materials cockroaches can’t cling to) and worked out a devious routine for sneaking the compartment into the hat. More trouble than the trick was worth? To you, probably. But not to magicians.
3. It’s hard to think critically if you’re laughing. We often follow a secret move immediately with a joke. A viewer has only so much attention to give, and if he’s laughing, his mind is too busy with the joke to backtrack rationally.
2012/2/18
The New York Times has a fascinating article about how retail companies use data mining and carefully targeted coupons to analyse and influence the spending habits of consumers, without the consumers getting wise to what's happening and resisting:
Almost every major retailer, from grocery chains to investment banks to the U.S. Postal Service, has a “predictive analytics” department devoted to understanding not just consumers’ shopping habits but also their personal habits, so as to more efficiently market to them. “But Target has always been one of the smartest at this,” says Eric Siegel, a consultant and the chairman of a conference called Predictive Analytics World. “We’re living through a golden age of behavioral research. It’s amazing how much we can figure out about how people think now.”A specific case the article describes is that of finding new parents-to-be, who will soon be in a position of having to form new spending habits, and doing so before the competition can identify them from public information; which is to say, inferring from statistical information whether a customer is likely to be pregnant, and at which stage, and then subtly manipulating her spending through the various milestones of her child's development:
The only problem is that identifying pregnant customers is harder than it sounds. Target has a baby-shower registry, and Pole started there, observing how shopping habits changed as a woman approached her due date, which women on the registry had willingly disclosed. He ran test after test, analyzing the data, and before long some useful patterns emerged. Lotions, for example. Lots of people buy lotion, but one of Pole’s colleagues noticed that women on the baby registry were buying larger quantities of unscented lotion around the beginning of their second trimester. Another analyst noted that sometime in the first 20 weeks, pregnant women loaded up on supplements like calcium, magnesium and zinc. Many shoppers purchase soap and cotton balls, but when someone suddenly starts buying lots of scent-free soap and extra-big bags of cotton balls, in addition to hand sanitizers and washcloths, it signals they could be getting close to their delivery date.
One Target employee I spoke to provided a hypothetical example. Take a fictional Target shopper named Jenny Ward, who is 23, lives in Atlanta and in March bought cocoa-butter lotion, a purse large enough to double as a diaper bag, zinc and magnesium supplements and a bright blue rug. There’s, say, an 87 percent chance that she’s pregnant and that her delivery date is sometime in late August. What’s more, because of the data attached to her Guest ID number, Target knows how to trigger Jenny’s habits. They know that if she receives a coupon via e-mail, it will most likely cue her to buy online. They know that if she receives an ad in the mail on Friday, she frequently uses it on a weekend trip to the store. And they know that if they reward her with a printed receipt that entitles her to a free cup of Starbucks coffee, she’ll use it when she comes back again.The uncanny accuracy of the algorithm is demonstrated by an anecdote about an angry father storming into a Target store demanding why they had sent his teenaged daughter coupons for nappies and prams, and then, some time later, returning to apologise, having discovered that she had, in fact, become pregnant.
Of course, there is the small issue of how to use this wealth of information in a plausibly deniable sense, without being obviously creepy. People, after all, tend to react badly to being surreptitiously watched and manipulated, especially so when deeply personal matters are involved:
“With the pregnancy products, though, we learned that some women react badly,” the executive said. “Then we started mixing in all these ads for things we knew pregnant women would never buy, so the baby ads looked random. We’d put an ad for a lawn mower next to diapers. We’d put a coupon for wineglasses next to infant clothes. That way, it looked like all the products were chosen by chance. And we found out that as long as a pregnant woman thinks she hasn’t been spied on, she’ll use the coupons. She just assumes that everyone else on her block got the same mailer for diapers and cribs. As long as we don’t spook her, it works.”
2011/12/7
What do you do if you're an oil company facing negative publicity over a controversial project like the Canadian tar sands? Well, you could always adopting the name of a much-loved company in another industry, as Paramount Resources Pixar Petroleum Corp. has done.
This is, of course, not the first example by far of an unpopular company changing its name (there has been Cheney-era mercenary company Blackwater renaming itself after a popular exchange-rate website, and carcinogenic drug dealers Philip Morris adopting the name Altria, a name which goes so far in the direction of heavy-handedly calculated benignness that it comes out the other end sounding appositely creepy), though as far as chutzpah goes, it might well set some kind of record.
2011/7/21
In the past, hand-made goods used to be considered inferior; cheap, flawed, jerry-rigged substitutes for expensive manufactured products. Nowadays, perfectly mass-manufactured goods are cheap, almost to the point of disposability. Hand-crafted items, meanwhile, have become signifiers of status, their flaws and imperfections representing individuality and artisanal values, in opposition to the alienatingly sterile qualities of assembly-line products. (That bag hand-sewn from drink containers by some dude in Berlin or Portland may not be as solidly made, well-designed or otherwise fit for purpose—in a prosaic, bourgeois way—as one manufactured in Shenzhen by the million, but what you lose in build quality and materials, you get back tenfold in the warm fuzzy feeling of being part of something outside the corporate-consumerist mainstream, i.e., differentiating yourself from the wrong kinds of white people who shop at Wal-Mart and eat at McDonald's.)
Writing in Make (a magazine of the maker culture—a new hobbyist culture with a focus on repurposing existing items, from cheap consumer electronics to flat-packed furniture, often for fun), Cory Doctorow speculates on how the corporations will attempt to commodify this trend, extrapolating from the already prevalent practice of having call centres in low-wage countries full of workers trained to pretend to be American/British/Australian to a vision of a manufactured replica of an anti-corporate maker counterculture, conjured out of the whole cloth using low-wage labour and business-process outsourcing methods:
Will we soon have Potemkin crafters whose fake, procedurally generated pictures, mottoes, and logos grace each item arriving from an anonymous overseas factory?
Will the 21st-century equivalent of an offshore call-center worker who insists he is “Bob from Des Moines” be the Guangzhou assembly-line worker who carefully “hand-wraps” a cellphone sleeve and inserts a homespun anti-corporate manifesto (produced by Markov chains fed on angry blog posts from online maker forums) into the envelope?If it happens, it won't be unprecedented. Ersatz authenticity (from studiedly shitty-looking advertiser-sponsored zines to ProTools plugins for making major-label alternative bands sound grungy and lo-fi) is big business.
2011/2/20
There may be (vast multitudes of) zombies among us online: leaked emails from US defense contractor HB Gary have revealed the existence of a system for managing large numbers of fake identities across social networks; the identities are created en masse with realistic pseudonyms and plausible character profiles and kept on life support with an automated or mostly automated system; the software has them retweet others' posts, or perhaps even uses natural-language processing to have them chime in minimally to comment threads ("I agree!"). Then, when they're needed, these zombie profiles can be pressed into service, flash-mobbing a forum with a dissenting view coming from a large number of real-looking people with authentic-looking histories, befriending real users on social networks for intelligence-gathering purposes, or similar; the operators have access to the record on the particular profile they're using, in order to avoid embarrassing faux pas:
To build this capability we will create a set of personas on twitter, blogs, forums, buzz, and myspace under created names that fit the profile (satellitejockey, hack3rman, etc). These accounts are maintained and updated automatically through RSS feeds, retweets, and linking together social media commenting between platforms. With a pool of these accounts to choose from, once you have a real name persona you create a Facebook and LinkedIn account using the given name, lock those accounts down and link these accounts to a selected # of previously created social media accounts, automatically pre-aging the real accounts.
Using the assigned social media accounts we can automate the posting of content that is relevant to the persona. In this case there are specific social media strategy website RSS feeds we can subscribe to and then repost content on twitter with the appropriate hashtags. In fact using hashtags and gaming some location based check-in services we can make it appear as if a persona was actually at a conference and introduce himself/herself to key individuals as part of the exercise, as one example. There are a variety of social media tricks we can use to add a level of realness to all fictitious personasHB Gary has been selling these to the US Government, presumably to intelligence and law-enforcement agencies; its imagined uses could range from allowing agents to infiltrate distributed protest groups for intelligence-gathering purposes to COINTELPRO-style disruption operations and psychological warfare. However, it's not unlikely that some version of this or similar software (either from them or another company) would end up in the hands of private corporations or other interests. Recently, HB Gary and two other defense contractors did recently pitch their services to the Bank of America, proposing disinformation attacks against WikiLeaks and its supporters. It could be argued quite robustly that collusion between the US intelligence establishment and corporations is a long-established tradition, dating back to ITT's involvement in the Chilean coup and the United Fruit Company's involvement in establishing the Guatemalan junta, so to imagine such tools in the hands of, say oil companies or agribusiness, being used to disrupt popular opposition, disrupt the organisation of trade unions, or even manufacture Tea Party-style pseudo-oppositional groups which support deregulation, is not a huge stretch. In the wild, it becomes just another tool to discreetly keep labour and environmental costs down. And then there's what happens when this filters down to the marketing departments. Or some guys in Russia make a clone of this and start selling it to scammers.
What about on the internet? Once the cat's out of the bag, people are going to be less trusting of strangers online. Until now, identifying a sockpuppet had been easy: if someone just joined a site, made no comments or a few content-free comments and then weighed in about why, let's say, smoking doesn't cause cancer or Silvio Berlusconi is the only honest man in Italian politics and the victim of a conspiracy, they were obviously a tentacle of some ham-fisted propaganda operation. Now, such a tentacle may have accounts on all major news sites, social networks and other services going back years, and a history of bland, neutral interactions with the online world. A retweet here, a few holiday photos (cropped/reedited from somebody else's Flickr pool, or a pool of content contributed by contractor employees) there, perhaps a few opinions about football or video games or mobile phones scattered around forums. Detailed conversation would be light, unless the operators pay humans (bound by oaths of secrecy more stringent than Amazon's Mechanical Turk service) to ride these zombies and have them form low-intensity relationships with actual random humans. (More high-intensity relationships could be risky, though given the recent revelations that Britain's secret police agents formed long-term romantic relationships with members of left-wing groups they were infiltrating, perhaps long-distance romances between zombie handlers in fluorescent-lit bunkers under Virginia or Alabama and lonely, emotionally volatile people around the internet could occur; perhaps these could even be exploited for operational uses, in the way Nigerian 419 scammers have done.) But the rest of us would be asking ourselves: what percentage of the people we interact with online—on newspaper forums, music discussion boards, dating sites, or of our Facebook friend circle—are actually real?
2011/1/17
GQ's website has a detailed account of last year's assassination in Dubai of Hamas leader Mahmoud al-Mabhouh, almost certainly by an elite Mossad hit squad, and the investigation that nailed down what happened, written up by Ronen Bergman, an Israeli journalist who writes about intelligence operations (and is the author of The Secret War With Iran):
At 6:45 a.m., the first members of an Israeli hit squad land at Dubai International Airport and fan out through the city to await further instructions. Over the next nineteen hours, the rest of the team—at least twenty-seven members—will arrive on flights from Zurich, Rome, Paris, and Frankfurt. They have come to kill a man named Mahmoud Al-Mabhouh, a Hamas leader whose code name within the Mossad—the Israeli intelligence agency—is Plasma Screen.
Then, in 2002, Prime Minister Ariel Sharon tapped Dagan, a former military commander with a reputation for ruthless, brutal efficiency, to restore the spy agency to its former glory and preside over, as he put it, "a Mossad with a knife between its teeth." "Dagan's unique expertise," Sharon said in closed meetings, "is the separation of an Arab from his head."Bergman pieces together a chronology of the operation and the investigation that followed, and a list of mistakes committed by the assassins which gave the Dubainese authorities enough to go on to produce a detailed account, all but pinning the operation on Israel.
The laughable attempts of the Mossad operatives to disguise their appearance made for good television coverage, but the more fundamental errors committed by the team had less to do with cloak-and-dagger disguises than with a kind of arrogance that seems to have pervaded the planning and execution of the mission.
2010/12/17
This year, consumers will be paying more for their Christmas turkeys, largely due to wheat prices having been pushed up by commodity traders speculating on them. Similar actions have brought hardship to the developing world, causing an additional 250 million people to go hungry in 2008, though for tremendous profit to those in the know.
Meanwhile, a recent WikiLeaks memo suggests that US and Spanish trade officials discussed artificially raising food prices to encourage adoption of genetically modified crops, breaking down those silly Europeans' opposition by hitting them in the hip pocket, and hopefully opening the door to a patent royalty windfall for US agribusiness.
2010/11/5
Elaborate disguise of the day: a young Hong Kong Chinese man boarded an Air Canada flight to Vancouver disguised as an elderly Caucasian man, by virtue of a latex mask:
The man changed out of the silicone mask during the flight, and was arrested on arrival in Canada; he has claimed refugee status.
The mask in question may be purchased from here, for US$689; it's said to be in low stock due to "extremely high demand".
2010/9/17
Dark Patterns is a list of deliberately deceptive or user-hostile website/interface design patterns, used by unscrupulous operators to deceive or exploit unwary users. These range from honest-but-hamfisted attempts to corral user behaviour into profitable channels (i.e., making it inconvenient to compare prices; sites which use JavaScript-based navigation to frustrate opening links in other windows do this) to various more underhanded tricks, ranging from sneaking unwanted items into shopping baskets, adding unsolicited recurring charges to spamming your friends under false pretexts to generally making it hard for the user to unsubscribe or do anything that reduces turnover. Featured offenders include the likes of Ryanair, various travel and consumer electronics retail sites, and Facebook (who get their own entry):
“The act of creating deliberately confusing jargon and user-interfaces which trick your users into sharing more info about themselves than they really want to.” (As defined by the EFF). The term “Zuckering” was suggested in an EFF article by Tim Jones on Facebook’s “Evil Interfaces”. It is, of course, named after Facebook CEO Mark Zuckerberg.
(via Boing Boing) ¶ 0
2010/9/12
A woman in Germany has been convicted of selling fake art forgeries. Petra Kujau sold forgeries of famous artworks, made by unknown forgers in Asia, to collectors, but attempted to pass them off as the work of famous forger Konrad Kujau (best known for the Hitler Diaries), netting €300,000 in total. She received a two-year suspended sentence.
2010/8/26
danah boyd has a new blog post on social steganography, or ways of encoding double meanings in messages one knows will be overheard.
Social steganography is one privacy tactic teens take when engaging in semi-public forums like Facebook. While adults have worked diligently to exclude people through privacy settings, many teenagers have been unable to exclude certain classes of adults – namely their parents – for quite some time. For this reason, they’ve had to develop new techniques to speak to their friends fully aware that their parents are overhearing. Social steganography is one of the most common techniques that teens employ. They do this because they care about privacy, they care about misinterpretation, they care about segmented communications strategies. And they know that technical tools for restricting access don’t trump parental demands to gain access. So they find new ways of getting around limitations. And, in doing so, reconstruct age-old practices.Often these techniques depend on shared cultural references; the fact that one's peers (typically within one's generation) have a shared vocabulary of song/movie/videogame/TV/&c. references has the convenient side-effect of providing a cryptolect that is all but parent-proof. (Which is why teens, i.e. those living in the totalitarian surveillance state of being a minor, are into ostensibly lame stuff like Justin Bieber and Fall Out Boy; few 'rents, even (or especially) those hip enough to know all about Joy Division and the Velvet Underground and krautrock and britpop and whatever, are going to study up on the latest godawful racket the kids these days are listening to just to be able to decode chatter most of which is going to be fairly inconsequential social administrivia. From which it might follow to say that when nostalgic adults listen to music from their adolescence, they are, knowingly or otherwise, revisiting the paraphernalia of strategies for mitigating a lack of freedom.) Anyway, boyd cites an example:
When Carmen broke up with her boyfriend, she “wasn’t in the happiest state.” The breakup happened while she was on a school trip and her mother was already nervous. Initially, Carmen was going to mark the breakup with lyrics from a song that she had been listening to, but then she realized that the lyrics were quite depressing and worried that if her mom read them, she’d “have a heart attack and think that something is wrong.” She decided not to post the lyrics. Instead, she posted lyrics from Monty Python’s “Always Look on the Bright Side of Life.” This strategy was effective. Her mother wrote her a note saying that she seemed happy which made her laugh. But her closest friends knew that this song appears in the movie when the characters are about to be killed. They reached out to her immediately to see how she was really feeling.It's debatable whether Monty Python counts as a parent-proof youth-culture reference. I'm guessing that the example story happened somewhere in the US, where Monty Python still has an aura of counterculture about it, and is likely to not be picked up by one's straight-laced 'rents. (Perhaps it happened in a devoutly Christian community, where The Life Of Brian would be virtually punk rock?)
Of course, nowadays Carmen could just have posted the update to Facebook under a filter, excluding her mother from seeing it, and her mother would have been none the wiser. (Unless Facebook has mechanisms preventing minors from hiding content from their parents, which I hadn't heard of.)
2010/6/30
In the US, the FBI recently arrested ten alleged Russian spies, who had been sent to the US in the 1990s, assuming American identities and attempting to befriend influential businessmen and weapons scientists. More details on the alleged spies (and more here); by all accounts, it seems that they weren't spectacularly successful at stealing secrets; one or two of them were better at milking their expense accounts, but others seemed to have lost the trust of their handlers; their tradecraft also seemed rather old-school, with the addition of a few new twists such as uploading data to surreptitious WiFi access points in cars. Meanwhile, David Wolstencroft, the creator of BBC spy series Spooks, describes the incident as Smiley's People with a laughtrack.
Some of the alleged spies took the cover of married couples; apparently they were paired up in Russia by their handlers and given their identities, before moving to America and actually having children together as part of their cover. The children are now in state custody, and their parents, should they end up in federal supermax prison or deported to Russia, are unlikely to see them again. I wonder whether hypothetical American sleeper agents abroad would go to quite that extent to maintain a cover or whether that degree of acceptance of individual sacrifice (both on the agents' part and that of the children brought into the world essentially as cover props) for a collective goal is specific to Russian culture.
Meanwhile, according to MI5, the number of Russian spies in London is up to cold war levels.
2010/6/21
Chinese companies looking to make an impression are now hiring random white guys to put on suits and play the parts of American/European business contacts:
Not long ago I was offered work as a quality-control expert with an American company in China I’d never heard of. No experience necessary—which was good, because I had none. I’d be paid $1,000 for a week, put up in a fancy hotel, and wined and dined in Dongying, an industrial city in Shandong province I’d also never heard of. The only requirements were a fair complexion and a suit.
“I call these things ‘White Guy in a Tie’ events,” a Canadian friend of a friend named Jake told me during the recruitment pitch he gave me in Beijing, where I live. “Basically, you put on a suit, shake some hands, and make some money. We’ll be in ‘quality control,’ but nobody’s gonna be doing any quality control. You in?”
2010/6/16
When North Korea played at the World Cup, part of the audience was its football fans. Only they weren't North Korean or football fans. The North Korean authorities decided that they couldn't risk the possibility of any North Koreans defecting once outside their national borders, and thus recruited Chinese "volunteers" to attend matches, play the roles of North Korean football fans and give the impression of North Korea being a normal country with sports fans who travel to follow their team. Only, being the kingdom of the world's last God-Emperor, they left nothing to chance; the volunteers were recruited individually by their government, and conductors were on hand to direct their cheering:
One Brazilian fan said: "I spoke with them. They had come from Beijing and knew nothing about football or the World Cup. They said they were supporting their Communist cousins and were happy to be there."
2010/6/15
A 1978 article on how to identify a CIA agent under diplomatic cover; back then, it was fairly easy to do so by simple techniques such as looking at US embassy personnel records and seeing who hangs out with whom at diplomatic dos.
Of course, they may well have tightened things up in the past 32 or so years.
- The CIA usually has a separate set of offices in the Embassy, often with an exotic-looking cipher lock on the outside door. In Madrid, for example, a State Department source reports that the Agency occupied the whole sixth floor of the Embassy. About 30 people worked there; half were disguised as "Air Force personnel" and half as State "political officers." The source says that all the local Spanish employees knew who worked on what floor of the Embassy and that visitors could figure out the same thing.
- CIA personnel usually stick together. When they go to lunch or to a cocktail party or meet a plane from Washington, they are much more likely to go with each other than with legitimate diplomats. Once you have identified one, you can quickly figure out the rest.
- The CIA has a different health insurance plan from the State Department. The premium records, which are unclassified and usually available to local employees, are a dead giveaway.
- The Agency operative is taught early in training that loud background sounds interfere with bugging. You can be pretty sure the CIA man in the Embassy is the one who leaves his radio on all the time.
2010/6/8
A discussion on Ask Metafilter about credit card fraud spawned a rather interesting comment from a former fraud detection department employee about what makes credit card transactions look suspicious:
Testing charges. These are usually online charges through known online vendors that a scammer can use to test a card number as valid. These have been mentioned before in the thread, but there were certain vendors that would fade in and out of popularity (I'm not naming names) that would allow very small (usually 1 dollar) charges on a card and produce some sort of digital product that allowed them to verify “yes this card works” or “no, this card is already being monitored”. They also told us that sometimes there were random guessing programs just trying to stumble across cards (as cards follow certain numbering rules, making it slightly more probable, and there being so many unused cards like college students get at football games and never touch). I'm not sure that I believe that last part, but that's what they told us. So Amazon MP3 followed by newegg... probably going to get called.
My first task was to take a look at the charge that specifically tripped the fraud alarm. I would look at it and first think to myself “Do they have a history of this?” I would compare this against demographics. An 80 year old woman who buys food for 6 months, and all of a sudden a charge coming through from steam? Probably not passing on that one. A 20 year old college student who charges everything from clothes to books, and then an iTunes purchase? Maybe they just got an iPod, I'll pass on it.
Cases weren't always cut and dried, so there's other things I can look at. I could see where plane tickets were purchased to and from. So if we have a plane ticket bought from BWI to LAX and sudden out-of-character charges for shopping in California, well... yeah, probably. I could see previous history through a comment log. Other operators (regardless of department) are obligated to comment each interaction with an account. For example, after working an account that I passed on I might write: “CHRGS COMING FROM OOS (out of state) BUT GAS TRAIL FROM HOME LOCATION TO CURRENT LOCATION PLUS HISTORY OF TRVL. N/A”
2009/9/11
Bizarre crime of the day: someone in Turkey kept nine young women captive in a house for around two months after convincing them that they were on a reality TV show. While there was no TV show, lascivious images of the women were sold on the internet:
They were made to sign a contract that stipulated that they could have no contact with their families or the outside world and would have to pay a 50,000 Turkish Lira fine ($A38,243) if they left the show before two months, the agency reported.
"We were not after the money but we thought our daughter could have the chance of becoming famous if she took part in the contest," the newspaper quoted one of the women's mother as saying. The paper identified her only by her first name, Remziye. "But they have duped us all."
2008/12/9
Now that he no longer needs the votes of the faith-based voters, outgoing president George W. Bush pretty much admits to not believing that religious stuff he earlier expounded:
Here's the précis: he does not believe in the literal truth of the Bible, did not invade Iraq because of his Christianity and does not believe his faith is incompatible with evolution. Bush will not even assert that the Almighty – who, he believes, is much the same one as is worshipped by other religions – chose him to become president.Remember that Jesus Camp documentary, in which kids from the red states were indoctrinated in Taliban-style facilities to believe that Bush is the instrument of God's will? Well, I'll bet there will be a lot of disillusionment there.
2008/11/7
A group of squatters has taken over an opulent property in Mayfair. The Da! Collective plans to turn 18 Upper Grosvenor St., a Grade 2-listed property near Hyde Park, the US Embassy and some of London's most expensive restaurants, into an art installation:
Behind the white pillars and imposing wooden door of the grade II-listed residence, the 30-plus rooms are now scattered with sleeping bags, grubby mattresses, rucksacks spilling over with clothes and endless half-finished art installations. While their neighbours' walls are lined with priceless paintings, No 18 now exhibits a room full of tree branches and another with a pink baby bath above which dangle test tubes filled with capers. Spooky foetuses line one fireplace.
hey had been watching the building for "at least six months" before they decided to try moving in, she said. "We had put tape on the keyhole, and kept looking through the letterbox to see if anyone had been there." Then, one October night, five of the group decided to go in. Some of them wore high-visibility jackets to look like builders; Smith had a clipboard and fur coat. They propped their rented ladder up against the front of the building, and one man climbed on to the dilapidated balcony. "I went across to the window and I couldn't believe it when it was unlocked," said the squatter, who declined to give his name. "I was so happy. We didn't really expect it to be open, so it was a really exciting moment."
The group has had a mixed reception from the other residents of Upper Grosvenor Street. "Our next-door neighbours have been really nice; they've even let us use their wireless internet," said Smith. Another neighbour, a man called Alexander, has offered the services of his maid to cook them food, she added.
From 7pm to 11pm, the Da! gang will be projecting images on to each of the 19 windows at the front of the squat. "It's going to look like a doll's house," said Smith, "and there is going to be a harpist and a cellist and performance artists."Under English law, the squatters (who have reconnected the electricity and claim to be maintaining the property and paying bills) are entitled to stay until they are formally evicted by the owners. These owners, a concern known as Deltaland Resources Ltd., based in the British Virgin Islands, do not seem to have made any attempt to contact the squatters; they have 11 years and 11 months to do so before the building legally becomes the property of the Da! Collective.
2008/10/26
Via Jim's blog, which I should really check more often: the New Yorker has an excellent article by John le Carré about how spies go mad.
2008/10/23
A 21-year-old Australian call centre employee is facing unspecified disciplinary action after taking sick leave and bragging on Facebook that he was absconding from work due to a hangover. Kyle Doyle's undoing seems to have been that, at some earlier time, he had added his boss to his friends list, which suggests that he might not have been the sharpest knife in the drawer; if you're looking for a partner to pull off the perfect crime with, he's probably not your man.
Heaping irony on top of stupidity, the snapshot of his profile that is circulating with the damning admission lists him as a supporter of the "Liberal Party of Australia", the right-wing party which introduced harsh industrial relations laws which, among other things, allow employers to demand medical certificates for as little as one day of sick leave.
2008/10/22
Nestlé, the food corporation whose name has been synonymous with unethical marketing of infant formula in the developing world, has been caught engaging in yet more dubious marketing practices abroad, this time when an ad for Maggi noodles, intended for Bangladesh, was mistakenly aired on a UK-based satellite channel, bringing it under the jurisdiction of the Advertising Standards Authority:
Shown on Nepali TV, the advert suggested that Maggi Noodles helped build strong bones and muscles. A boy playing tug-of-war with his friends ran in to see his mother, who explained to him: "Maggi is the best because it has essential protein and calcium that help to build strong muscles and bones." On-screen graphics depicted a yellow glow over a bicep and a knee, implying that those areas of the body were helped by the product.
In a statement, Nestle said: "We rigorously ensure that all health claims made on Nestle products comply with local legislation. The advert had been approved for broadcast and complied with the necessary legal requirements in Bangladesh, the market the advertisement was intended for. "It was never intended for transmission in the UK."
2008/10/10
Academic paper of the day: The Dining Freemasons, or a look at the mechanics and problems unique to secret societies from the perspective of (computer) security protocols:
To a first approximation, a secret society has three functions:The paper talks about steganographic broadcasts (i.e., transmitting your affiliation in a coded form; the drawing of a fish by early Christians is one famous example), plausible deniability, and suggests various protocols using the semantic meanings of bodies of knowledge known to the society, including coding challenges and responses (or even small amounts of information) in the truth value of statements about the shared text.Each area presents intriguing challenges, but crucial to each aspect is membership testing – society members must be able to identify each other in order to pass on the doctrine, to confer rewards and to consider new applicants.
- to recruit the worthy,
- to pass on a secret doctrine,
- and to reward its members.
Also from the same authors: A Pact With The Devil, or a hypothetical outline of how a genuinely nasty form of malware could use various forms of persuasion and blackmail to spread itself.
2008/10/8
Russia's ever-ingenious con artists have come up with another clever scam: fake iPhones. The devices look exactly like real iPhones with depleted batteries, and when activated show the Apple booting screen. They're handed over to the mark as collateral for borrowed money; the mark sees that the phone appears to start to boot, and assumes that the battery is depleted. When the borrower doesn't return to pick it up (and, presumably, the contact details they left turn out to be bogus), the mark takes it down to a service centre, where the technicians open it up and find that it's a plastic shell containing two batteries, a LED and a segment of a steel bar for weight.
I'm guessing that the reason the scam works is because most people wouldn't believe that someone would go to the trouble of making something that looks exactly like an iPhone but is cheap enough to be discarded for less than the value of one.
2008/10/4
This is ingenious: a bank robber in Washington state made his escape after putting an ad on Craigslist for people to (unwittingly) act as decoys:
"I came across the ad that was for a prevailing wage job for $28.50 an hour," said Mike, who saw a Craigslist ad last week looking for workers for a road maintenance project in Monroe.
He said he inquired and was e-mailed back with instructions to meet near the Bank of America in Monroe at 11 a.m. Tuesday. He also was told to wear certain work clothing. "Yellow vest, safety goggles, a respirator mask… and, if possible, a blue shirt," he said.
Mike showed up along with about a dozen other men dressed like him, but there was no contractor and no road work to be done. He thought they had been stood up until he heard about the bank robbery and the suspect who wore the same attire.I wonder whether they'll catch him. Or, indeed, whether others will adapt such an idea. Perhaps we'll see a rash of robberies and heists, using spontaneous zombie flashmobs, "secret" rock concerts, Anonymous-style masked protests or other such pretexts as smokescreens.
2008/10/1
In September of last year, millionaire adventurer Steve Fossett took off on a routine solo flight in Nevada, in near perfect conditions, and was never seen again. Extensive searches revealed no wreckage and no trace of him, and he was declared dead in February. Now claims are emerging that he may have faked his death:
The faked-death story goes as follows. In the months leading up to his death, Fossett may have been leading what breathless news reports describe as "a secret double life".
As Fossett's many previous collaborations with Sir Richard Branson suggest, he was a born showman, meticulous about maintaining a gilded public image. According to the faked death theory, disappearing off the face of the earth would allow him to avoid both fates – while leaving a fitting personal legacy after a swashbuckling career that had started to enter its teatime years.
According to the case against Fossett, the plane he was flying might also have been designed to make a rescue operation difficult. Most of its lightweight structure is invisible to radar and infrared detectors. It is also easily dismantled and hidden.Update: They found the wreckage of Fossett's plane; they're still searching for remains.
2008/9/18
The US election season is proving a bonanza to scientists studying deception, from incongruous body language to the vague phraseology of "spin":
BLINK and you would have missed it. The expression of disgust on former US president Bill Clinton's face during his speech to the Democratic National Convention as he says "Obama" lasts for just a fraction of a second. But to Paul Ekman it was glaringly obvious.
"Given that he probably feels jilted that his wife Hillary didn't get the nomination, I would have to say that the entire speech was actually given very gracefully," says Ekman, who has studied people's facial expressions and how they relate to what they are thinking for over 40 years.Another algorithm scores politicians on the amount of spin, or manipulative content-free language, in their speeches, using word frequencies:
The algorithm counts usage of first person nouns - "I" tends to indicate less spin than "we", for example. It also searches out phrases that offer qualifications or clarifications of more general statements, since speeches that contain few such amendments tend to be high on spin. Finally, increased rates of action verbs such as "go" and "going", and negatively charged words, such as "hate" and "enemy", also indicate greater levels of spin. Skillicorn had his software tackle a database of 150 speeches from politicians involved in the 2008 US election race (see diagram).
In general though, Obama's speeches contain considerably higher spin than either McCain or Clinton. For example, for their speeches accepting their party's nomination for president, Obama's speech scored a spin value of 6.7 - where 0 is the average level of spin within all the political speeches analysed, and positive values represent higher spin. In contrast, McCain's speech scored -7.58, while Hillary Clinton's speech at the Democratic National Convention scored 0.15. Skillicorn also found that Sarah Palin's speeches contain slightly more spin than average.So whilst Obama is one slick player, the straight-talkin', plain-dealin' McCain has little to rejoice about, according to a different metric:
"The voice analysis profile for McCain looks very much like someone who is clinically depressed," says Pollermann, a psychologist who uses voice analysis software in her work with patients. Previous research on mirror neurons has shown that listening to depressed voices can make others feel depressed themselves, she says.
Additionally, McCain's voice and facial movements often do not match up, says Pollermann, and he often smiles in a manner that commonly conveys sarcasm when addressing controversial statements. "That might lead to what I would call a lack of credibility."
2008/9/17
A Pentagon researcher has laid out a chilling possibilities: that terrorists could be using online role-playing games to plan attacks, disguised as raids in the virtual world:
In it, two World of Warcraft players discuss a raid on the "White Keep" inside the "Stonetalon Mountains." The major objective is to set off a "Dragon Fire spell" inside, and make off with "110 Gold and 234 Silver" in treasure. "No one will dance there for a hundred years after this spell is cast," one player, "war_monger," crows.
Except, in this case, the White Keep is at 1600 Pennsylvania Avenue. "Dragon Fire" is an unconventional weapon. And "110 Gold and 234 Silver" tells the plotters how to align the game's map with one of Washington, D.C.Of course, the same argument could apply to any form of discussion. Terrorists could just as easily use last.fm playlists or online mixtapes to hatch their plans. (The above plan could be encoded as a copy of OMD's Enola Gay and a song by industrial noise band Whitehouse, followed by a song exactly 11 minutes long, which would give the time of the attack. For chemical or biological weapons, replace Enola Gay with Britney Spears' Toxic. You get the idea.) Or they could use internet memes; who's to say that the particular spelling/grammatical anomalies on the caption of the latest set of cat photos don't encode the details of a planned terrorist attack?
Of course, the terrorists could even eschew the internet altogether, using other means of communicating their plans, such as, say, public art. Who's to say that a terrorist sleeper agent hasn't been quietly making a name for himself as an artist, getting lucrative commissions, and waiting for the order to encode doomsday plans in a public sculpture (plenty of opportunity there) or a semi-abstract mural. (Avant-garde art itself is too easy.) Or architecture, or urban planning (if there are Masonic symbols in the layout of Washington DC's streets, there could be other things elsewhere.) The possibilities are infinite.
Perhaps Bruce Schneier could make his next Movie Plot Threat Contest hinge on coming up with creative ways in which evildoers could go to elaborate lengths to encode the message "nuke the Whitehouse at 11:00" in innocuous-looking environments. Because, as we all know, supervillains love complexity in and of itself, and the ideal terrorist plan would look more baroque than a steampunk laptop on Boing Boing.
2008/9/8
A Japanese expert on North Korea claims that the secretive cult-state's God-Emperor Kim Jong-Il died of diabetes in 2003, and has since been played by several doubles, who have made public appearances and conducted international negotiations in his guise:
He believes that Kim, fearing assassination, had groomed up to four lookalikes to act as substitutes at public events. One underwent plastic surgery to make his appearance more convincing. Now, the expert claims, the actors are brought on stage whenever required to persuade the masses that Kim is alive.
One of its principal claims is that a voiceprint analysis of Kim’s speech at a 2004 meeting with Junichiro Koizumi, then the Japanese prime minister, did not match an authenticated earlier recording.If this is true, who controls the doubles? Do they rule the country themselves like some kind of freakish quadrumvirate, or are they kept under control by some shadowy true leader?
Also, it should be noted that, if this is true, it's not as great a leap as one might think. North Korea's "Great Leader" remains the late Kim Il-Sung; Kim Jong-Il (whilst officially credited with godlike powers) is merely the "Dear Leader", serving as a sort of viceroy in the absence (and the spectral shadow) of his father. If KJI has now popped his clogs, that merely takes it one step further.
So now North Korea is ruled by two godlike beings not present on this Earth, or rather by their representatives, and is essentially a somewhat novel theocracy. One could probably call it a necrocracy.
2008/8/18
The Chinese government has hit upon a novel solution for preventing troublesome protests from erupting at Olympic events: surreptitiously lose most of the tickets, and bus in well-disciplined cheer squads to fill the empty seats, taking place of unpredictable members of the public:
Blocks of tickets went to government departments, Communist party officials or state-owned companies, which have quietly obeyed orders not to hand them out. “People are so angry because they slept all night outside ticket booths and got nothing and now they see this,” said one blogger, Jian Yu.
At some football matches in the northern city of Shenyang, only a third of the seats were taken. Even some gymnastics finals, usually one of the biggest attractions on the programme, were not sold out.Of course, people who waited for tickets but failed to get them (from ordinary Chinese sports fans to the relatives of foreign competitors) are rather annoyed, though they are assuming that the purpose of the Olympics is to provide an entertaining spectacle (or, alternately, to serve as a promotional exercise for corporate sponsors). The Chinese government's view of the Games' purpose is somewhat different: to buy legitimacy for a worrisomely totalitarian one-party state (one typically associated with doing unspeakable things to cuddly
And here is Charlie Brooker's take on it.
2008/8/17
A few weeks ago, a man by the name of Clark Rockefeller entered the news, after having abducted his daughter who was visiting him in Boston. Not much was mentioned about him, except that he was not believed to be related to the famous oil family. Gradually, an increasingly bizarre story emerged. "Clark Rockefeller", it seemed, was a German man named Christian Gerhartsreiter, who left for America at the age of 17 in 1978 to seek his fortune. Along the way, he tried (unsuccessfully) to get into acting in Hollywood, before discovering that his true talent lay in fashioning new identities and stories for himself, always coming up with a new one when his inevitably grandiose and narcissistic claims (or, in one case, quite possibly murdering his landlord) compromised his current one. He became Christopher Chichester, a British aristocrat who was moving his castle to America, then Christopher Crowe, a Wall Street stockbroker, and finally Clark Rockefeller, brilliant mathematician/physicist and scion of fabulous old money; along the way, a family he was renting from in California disappeared (unidentified remains were found under their house a decade later), and later, "Christopher Crowe" tried to sell their old truck, making a hasty exit to rescue his parents who had been kidapped in South America before the police could question him. Not to mention thad he lost his stockbroking job after using the social security number of the Son of Sam serial killer on his licence application.
Anyway, Gerhartsreiter is now in custody and has been identified as such. I imagine he'll have a much harder time getting away this time.
2008/7/22
The big news today was that Radovan Karadzic, the Bosnian Serb warlord wanted for organising massacres of Croatian and Muslim civilians, has been arrested, and is likely to be shipped to The Hague post-haste. Rather than hiding in a hole or an impregnable fortress manned by fierce hordesmen, Karadzic spent the past 14 years being a celebrated New Age therapist in Belgrade. He grew an ecclesiastical-looking white beard, called himself Dragan Dabic and went around teaching meditation, yoga and tai chi and offering "bio-energy healing", amassing a considerable following.
Those who knew Dr Dabic on the New Age circuit have told The Times that he was regarded as an expert in silence and meditation. One of his lectures was called 'The relationship between calmness and meditation,' and another one was titled 'How to nurture your own energies.'
Mr Ljajic said that Dr Karadzic's disguise had rendered him so unrecognisable that even the landlord from whom he rented a flat had no idea who he really was.
2008/6/6
 A nursing home in Düsseldolf has come up with a novel way of dealing with stray Alzheimer's patients; they set up a fake bus stop outside the home:
A nursing home in Düsseldolf has come up with a novel way of dealing with stray Alzheimer's patients; they set up a fake bus stop outside the home:
“It sounds funny,” said Old Lions Chairman Franz-Josef Goebel, “but it helps. Our members are 84 years-old on average. Their short-term memory hardly works at all, but the long-term memory is still active. They know the green and yellow bus sign and remember that waiting there means they will go home.” The result is that errant patients now wait for their trip home at the bus stop, before quickly forgetting why they were there in the first place.
(via Boing Boing) ¶ 1
2008/5/1
Recently, Australia's recording industry body released a video, made for schools, in which various popular musicians (from industry stalwarts to the hottest commercial-indie bands today) talking about how file sharing is hurting them. Now one of the particupants—Lindsay McDougall, the guitarist from JJJ alternative band Frenzal Rhomb—has issued a statement that he was misled into appearing in the video, and doesn't actually disapprove of file sharing:
He said he was told the 10-minute film, which is being distributed for free to all high schools in Australia, was about trying to survive as an Australian musician and no one mentioned the video would be used as part of an anti-piracy campaign.
McDougall said: "I have never come out against internet piracy and illegal downloading and I wouldn't do that - I would never put my name to something that is against downloading and is against piracy and stuff, it's something that I believe is a personal thing from artist to artist."
"I would never be part of this big record industry funded campaign to crush illegal downloads, I'm not like [Metallica drummer] Lars Ulrich. I think it's bullshit, I think it's record companies crying poor and I don't agree with it."
"I'm from a punk rock band, it's all about getting your music out any way you can - you don't make money from the record, the record companies make the money from the record. If they can't make money these days because they haven't come onside with the way the world is going, it's their own problem."Other artists were unable to be contacted for comment.
2008/4/4
Today's words of advice: should you ever decide to burgle a funeral parlour, it is advisable to dress the part, so that, should you be interrupted, you can blend in with the customers, unlike this guy:
Police officers arrived with the owner, and eventually found the suspect lying on a table in a glassed-in chamber used for viewings of deceased people during wakes, a local police official said from Burjassot.
"The custom here is for dead people to be dressed in suits, in nice clothes that look presentable. This guy was in everyday clothes that were wrinkled and dirty," the police official said.Also, should you have the dubious fortune to be nicknamed after a weapon of mass destruction, don't write your nickname on any items you may leave lying around.
(via Boing Boing) ¶ 0
2008/3/31
The colossal, ongoing cock-up of Heathrow's new Terminal 5 has been a boon to London's homeless community, who have taken to disguising themselves as delayed travellers and sleeping in the terminal:
Each night, scores of London's homeless men and women take advantage of modern travel delays by posing as stranded passengers in order to sleep in a warm and safe place. They play a cat-and-mouse game with police, often donning floral shirts, fanny packs and other travel accessories to blend in. And their increasing creativity — and ability to disappear in Heathrow's swelling crowds of delayed passengers — has prompted the airport to try a new approach.
"Rough sleepers," as homeless people are known in Britain, disguise themselves at all major airports, says Sandie Cox of Heathrow Travel Care, the social care organization overseeing the one-year pilot scheme. Indeed, Chicago's O'Hare airport instituted a homeless outreach in the 1990s. But while the problem may not be unique to Heathrow, several factors make it easier for rough sleepers to blend in. It is the busiest airport in Europe, has more delays than other major hubs, and while it doesn't serve Europe's low-cost carriers, it has still seen the effects of the democratization of air travel: gone are the days when you could identify a British air passenger by their suit and shiny shoes. Indeed, on Wednesday, the two scruffy passengers curled in the corner of a remote bathroom turned out to be holding tickets to LAX; they had chosen their spot because it was the only place they could find an outlet to charge their hand-held video game console.
2008/3/30
Griefers attack epilepsy forum, post flashing GIFs, trigger seizures, showing that they've totally pwn3d those epileptics (who presumably deserve it because epileptics are totally ghey or something). Looking further into it, the following detail emerges:
Circumstantial evidence suggests the attack was the work of members of Anonymous, an informal collective of griefers best known for their recent war on the Church of Scientology. The first flurry of posts on the epilepsy forum referenced the site EBaumsWorld, which is much hated by Anonymous. And forum members claim they found a message board thread -- since deleted -- planning the attack at 7chan.org, a group stronghold.A lot of people are saying that this attack was actually planted by Scientologists seeking to discredit Anonymous, an utterly cynical and callous course of action that, given the Church of Scientology's "Fair Game" policy, does not seem entirely inconsistent with the organisation's history. Though others (in threads such as this one) are pointing out that, before Anonymous took up the anti-Scientology banner and restyled themselves as champions of those victimised by sinister cults, they were essentially a collective of sadistic sociopaths who did a good line in griefing less publically acceptable targets, going well beyond spamming forums with Goatse images and into actual stalking (massively distributed), death threats and highly targeted psychological warfare.
Another possibility: what it the rabbit hole goes deeper, and the whole Anonymous anti-Scientology campaign was engineered by the Church of Scientology to reclaim the moral high ground, discredit critics of their organisation by association, and perhaps even undo some of the damage to their image that Tom Cruise's increasingly bizarre behaviour has done? If so, then it was impeccably timed; the anti-Scientology protests hit the media, latching onto adorably innocuous internet memes (LOLCats, rickrolling) to get maximum traction, and overshadowing a decade of boringly thoughtful criticism of the CO$; with the church's feeble anti-Anonymous campaigns being little more than tinder to parodists, soon Anonymous was equated in the public's eye with criticism of That Weird, Creepy Celebrity Religion. Enough time passed for this to sink in, and then this, and looking into Anonymous/4Chan's history reveals that, actually, they are sadistic sociopaths. Suddenly, rubbishing the Church of Scientology (however justifiedly) seems in rather poor taste, much in the way that toothbrush mustaches were after 1945.
2008/3/27
Someone is sending pro-Tibet groups documents infected with keylogging malware, configured to send back keystrokes to a server in China. The documents are sent from addresses forged to resemble human rights groups, and purport to be details of Chinese massacres in Tibet and similar information.
The exploit silently drops and runs a file called C:\Program Files\Update\winkey.exe. This is a keylogger that collects and sends everything typed on the affected machine to a server running at xsz.8800.org. And 8800.org is a Chinese DNS-bouncer system that, while not rogue by itself, has been used over and over again in various targeted attacks.
The exploit inside the PDF file was crafted to evade detection by most antivirus products at the time it was sent.
Somebody is trying to use pro-Tibet themed emails to infect computers of the members of pro-Tibet groups to spy on their actions.Of course, the pro-Tibet groups could avoid being pwn3d by the Chinese by the simple expedient of not using Windows or common software to open documents.
2008/2/8
Looks like Microsoft is up to its old tricks: the latest AJAX-enhanced version of Hotmail refuses to work if the web browser identifies itself as Firefox 2; if one reconfigures it to identify itself as Internet Explorer, it works perfectly. What does this mean? Well, given that Microsoft are likely to buy Yahoo! (a lot of analysts now rate Yahoo!'s chances of escaping their clutches as slim), taking control of Flickr and del.icio.us, those who use those sites from non-Windows, non-IE platforms, and with non-Microsoft web applications, have yet more reasons to feel uneasy.
2008/1/30
A piece on counter-surveillance tactics used by terrorist suspects. In summary, they go out of their way to appear assimilated and un-religious, discuss plans in remote wilderness locations or online pornography sites (what, no Second Life/World of Warcraft?), use Skype (which is difficult to tap) and speak in code:
Wiretap transcripts and other court records show that the cell of North African immigrants tried hard to blend into Italian society, working regular jobs, sending their children to public schools and taking pains not to appear unusually religious. When they did talk on the phone, they often adopted a roundabout or obtuse manner that masked their real meaning.
"Taxi drivers," Redouane el Habab said, referred to suicide bombers; explosives were "dough." Anybody who had to go to "the hospital," he added, had been taken to jail, while those visiting "China" were really attending training camps in Sudan.
2008/1/13
Details of how the NSA hacked cryptography machines from Swiss company Crypto AG, inserting an undetectable security hole which allowed them to read the traffic of users (including Iranian government orders to assassins and terrorists including the Lockerbie bombers):
On the day of his assassination and one day before his body was found with his throat slit, the Teheran headquarters of the Iranian Intelligence Service, the VEVAK, transmitted a coded message to Iranian diplomatic missions in London, Paris, Bonn and Geneva. "Is Bakhtiar dead?" the message asked.
"Different countries need different levels of security. The United States and other leading Western countries required completely secure communications. Such security would not be appropriate for the Third World countries that were Crypto's customers," Boris Hagelin explained to the baffled engineer. "We have to do it."
Juerg Spoerndli left Crypto AG in 1994. He helped design the machines in the late '70s. "I was ordered to change algorithms under mysterious circumstances" to weaker machines," says Spoerndli who concluded that NSA was ordering the design change through German intermediaries.
The ownership of Crypto AG has been to a company in Liechtenstein, and from there back to a trust company in Munich. Crypto AG has been described as the secret daughter of Siemens but many believe that the real owner is the German government.
2006/6/27
Global advertising agency Saatchi & Saatchi have unveiled the latest breakthrough in making advertising ever more deceptive, intrusive and intelligence-insulting: the stick-on door peephole diorama:
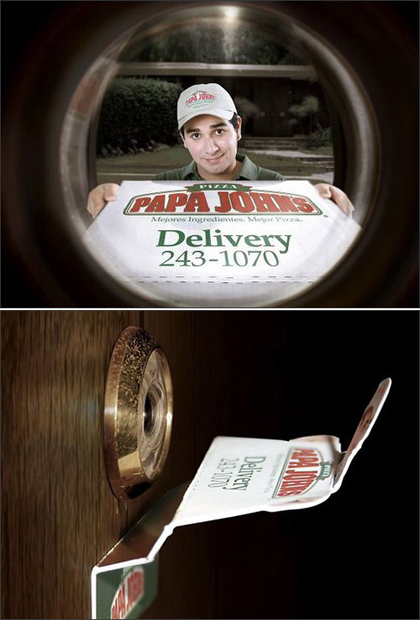
The original intended use is for getting people who don't think critically to buy more crap, though given Gibson's Law ("the street finds its own uses for things"), it could be only a matter of time before muggers/home-invaders start using the technology.
2005/10/6
An interview with James Freedman, an illusionist and white-hat pickpocket who was employed as a consultant for the film Oliver Twist:
Freedman gives me his jacket to put on. In the inside pockets are two wallets and two pens. Keeping eye contact, he asks what I have in my jeans pockets. I show him some keys and replace them. During those few seconds, he nicks the wallets and pens. As I'm reacting to this first loss, he manages to extract the keys out of my backpocket. I don't see a thing.
It's embarrassing. I knew what he was going to do and yet he still managed to fleece me. I don't even have the excuse of a natural distraction, which, Freedman says, is what pickpockets look out for. "At Westminster Tube station," he says, "the first thing people do when they come out is look at Big Ben." And, of course, thieves love the posters in the Tube that warn people to safeguard their belongings "because people show you where their things are when they pat them."
2005/9/20
Blogging ambulanceman Tom Reynolds on how to tell if someone's faking unconsciousness:
The easiest, and quickest way to see if someone is faking unconsciousness is to lightly brush your finger against their eyelashes. If their eyes flicker, then they are almost certainly faking it. Also if they try to keep their eyes closed when you try to open them, they are definitely faking it. Another way of checking is to hold their hand over their face, and let it drop. People tend to be reluctant to let their hand hit them on the nose, and so the hand will instead magically drop to one side.
My favourite tale of how to uncover a pretender in a hospital setting was a doctor, who would loudly ask for the 'brain needle', to draw off some brain fluid from the unconscious patient via the ear. Of course, he would continue, the patient needed to be unconscious because otherwise they might flinch and the needle go into the brain itself. This was normally followed by the patient 'waking up' and asking, "Doctor, where am I?".
2005/7/29
Psychologists are now looking at magic tricks for answers to how the mind works. Developed and refined over centuries, such tricks and techniques are now being recognised as containing a lot of folk knowledge about the low-level workings of consciousness and perception:
A card trick that lasts four or five minutes, for example, might have 20 pages of detailed text to describe exactly where to look, what to say, what to do and so on. And a lot of the understanding of a trick has to be from the perspective of the audience.
Our brains filter out a huge amount of the mass of sensory input flooding in from our environment. Kuhn explains that we see what we expect to see and what our brains are interested in. "Our visual representation of the world is much more impoverished than we would assume. People can be looking at something without being aware of it. Perception doesn't just involve looking at an object but attending to it."
2005/7/26
Scientists in Switzerland have developed a robot cockroach convincing enough to infiltrate cockroach societies and subvert them from within, with the other roaches never twigging to the fact that their new companion was a robot:
That's part of what the scientists have been successful at showing with InsBot. In their latest experiment, the miniature robot drew the group of insects from a darkly lighted den to a more lit location, despite the roaches' affinity for low lighting. The roaches followed InsBot for the companionship.
Scientists believe that if they can use robots to mimic and respond to animals then they could eventually control the animals' behaviour. For example, they could use robots to stop sheep from jumping off cliffs or to migrate cockroaches out of infested homes. Progress in the field could ultimately influence and aid in scientific fields like medicine, agriculture and ethology (which is the study of animal behaviour).
2005/6/13
The next advance in Total Information Awareness (or whatever it's called) may be a technique, currently being developed in Canada, to detect suspicious activity by the absence of keywords in email; this is more sophisticated than looking for keywords in emails (as the NSA was believed to have been doing since the days of UUCP):
One difference might be the complete absence of words someone might possibly think would draw a law enforcement agencys attention to their e-mails, but that most people would occasionally use innocently (as in "my presentation yesterday really bombed".) Another, Skillicorn says, is that research shows people speak and write differently when they feel guilt about a subject, for instance using fewer first-person pronouns, like I and we. "If you're up to no good", he says, "it's very hard for you to write something that looks ordinary."
Skillicorn doesn't know all the ways suspicious e-mails might read differently from innocent ones. The beauty of his approach is that he doesn't need to know. His software is designed simply to look for messages that are different, based on word frequencies, from the mass of e-mails. It neednt understand the reasons for the differences.So, when this technology matures (assuming that the will is there, which if it isn't now, it will probably be in a few terrorist outrages' time), we can expect, at the heart of ECHELON or similar, supercomputers tracking the email traffic of individuals (by email address, IP number or possibly a cluster of identifiers) and monitoring them for variations; as soon as an individual's behaviour changes microscopically (regardless of what it changed from and to; this works much in the way that highly-skilled readers of body language such as TV mentalist Derren Brown can detect truthfulness or lies by familiarising themselves with natural patterns and watching for deviations), they can be flagged for review. This could detect conspirators, criminals or other deceivers (right down to people planning surprise parties for loved ones, or trying to conceal embarrassing secrets), or possibly other shifts in mental state (depression, anxiety and such). The possibilities of such a technology extend beyond merely catching potential terrorists (or paedophiles, or MP3 pirates, or tax avoiders, or pro-democracy activists, depending on jurisdiction); I imagine that, for one, intelligence agencies with access to it could use it for pinpointing the weakest links in organisations they are targetting for infiltration, or otherwise use it to flesh out psychological profiles.
Elsewhere in the article, it mentions the possibility of detecting telltale patterns of activity by traffic analysis alone, and mentions that the infamous Enron email collection is not particularly useful for such research because those sending the emails didn't actually try to pretend that they were doing anything other than screwing people over.
2005/3/29
A look at the U.S. Secret Service's tools for breaking encryption on seized data. Not surprisingly, they use a network of distributed machines to help brute-force keys. Cleverly enough, before they do so, they assemble a custom dictionary of potential keys/starting points from all data on the seized machine (including files, web browsing histories, and presumably terminology associated with the areas of interest visited web sites relate to). (via /.)
"If we've got a suspect and we know from looking at his computer that he likes motorcycle Web sites, for example, we can pull words down off of those sites and create a unique dictionary of passwords of motorcycle terms," the Secret Service's Lewis said.
Hansen recalled one case several years ago in which police in the United Kingdom used AccessData's technology to crack the encryption key of a suspect who frequently worked with horses. Using custom lists of words associated with all things equine, investigators quickly zeroed in on his password, which Hansen says was some obscure word used to describe one component of a stirrup.
This technique apparently works surprisingly well, because people (including organised criminals) tend to choose relatively predictable passwords.
The moral of this story is: if you're planning the perfect crime using computers and encryption, you may find it wise to develop an obscure interest and not mention it by electronic means. Or, for that matter, let it show up in credit card receipts, library records, personal effects, or any other information the authorities could get. Which could be trickier than it sounds.
Also on the subject of people subconsciously giving away more than they think: this IHT article on "psychological illusionist" Derren Brown (via bOING bOING):
He produces a sheet of blank paper and issues an instruction: Draw a picture. "Try to catch me out; make it a bit obscure," he orders. "Don't draw a house; don't draw a stick man." Walking to another room and out of sight, he decrees that the picture should be concealed until the end of the interview - whereupon, he claims, he will reveal what it is.
Recently, he said, he used his talents to defuse a situation in which an aggressive youth approached him on the street, yelling, "What are you looking at?" (Brown responded with a rapid series of diversionary non sequiturs, he said; the man burst into tears.)
Instructing me to concentrate, he pulls out a blank sheet of paper and begins sketching, chatting all the while. He tells me he "sees" a conical shape with spots on it - some sort of decorated lamp with a blob on top. And knock me down if he does not produce a near-exact replica of my drawing, the only differences being that his has more dots than mine, and his stripes are horizontal, not vertical.
Channel 4 has a Derren Brown microsite here, with streaming video and explanations of some of the tricks (such as making people fall asleep in phone booths). Think of it as the human equivalent of the buffer overrun attack.
2005/1/12
Two Dutch designers are taking on the growing menace of muggers with handbags embossed with outlines of guns; they also have ones with the shapes of knives and crucifixes (the last are presumably for use against vampires), not to mention laptop bags embossed with groceries to make them look less stealable. (Not sure how well that works; the outlines in the photos look a bit too cartoonish and unrealistic. I imagine that simple non-rectangular lumpiness, of the "I'm carrying lots of soft, non-valuable things", would probably be more effective in practice.) (via bOING bOING)
2005/1/5
One of Britain's leading "visual merchandising consultants" reveals the psychological tricks used by shops to get people to buy stuff: (via Mind Hacks)
Most of the prices in electrical stores end in.99p. But a few end in.98p or 95p. That's a signal that a product is old stock and needs to be sold quickly. If you're foolish enough to ask a sales assistant for advice in a big electrical chain, the loyal staff will steer you towards these.
Table tops positioned next to racks allow women to handle the trousers and tops. "Younger women like scruffed-up clothes displays it suggests that these are popular. If the piles seem too neat, then obviously no one else is buying these items. Older women are more exacting in their standards."
2004/10/7
Police in Hampshire have used a fake game show to arrest various offenders (mostly common neds, by the sound of it) they had been looking for. The offenders, ranging from fine-dodgers to those wanted for common assault, were sent letters inviting them to appear on a game show with the chance of winning large prizes. The police then set up the event at Portsmouth Guildhall, going to great lengths to do so, even hiring former crooked Tory MP turned celebrity Neil Hamilton and his wife to present the show: (via Found)
As the "guests" arrived they were frisked and had their identities checked by a police officer dressed in a dinner suit. After having their make-up done, the contestants waited backstage where they could hear the sound of a taped studio audience. One by one they were called on to the stage, along a red carpet, through a cloud smoke and straight into the hands of two awaiting police officers.
This event, which is already being decried by civil libertarians, will be broadcast on the UK's Channel Five (the same fearless bastion of the public's right to know that recently got David Beckham's alleged lover to masturbate a pig on air.)
2004/5/7
The clown prince of the American Left, Michael Moore, claimed a few days ago that Disney killed the distribution of his most recent film, Fahrenheit 911, to preserve tax breaks in Florida; a classic case of corruption, cronyism and corporate power suppressing free speech. Or it would be, if it wasn't an outright publicity stunt. Moore, it seems, knew all along that Disney had no intention of distributing his film, though found it more advantageous to strategically misrepresent the situation as Disney doing the Bush Junta's dirty work. The existence of the alleged tax breaks is also up for some debate. Then again, as Mel Gibson discovered, there's no such thing as bad publicity.
2004/4/9
I just watched a DVD of Nine Queens, an Argentine heist film about two swindlers (one vaguely seedy veteran and one naïve but talented rookie he takes under his wing) trying to pull a high-stakes scam involving a sheet of ostensibly rare stamps and a collector, set against the backdrop of Buenos Aires. The film was fast-paced, and it seemed that each moment, some new detail or layer was unfolding (from crooked officials wanting their take to the scammers trying to psych each other out of their respective cuts, to things changing at the last minute, and the ever-present question of who is playing a deeper game and what is really happening). I found it quite gripping and enjoyable.
2004/4/7
Birthday greetings ...prison-style! Or, how gang members can't resist sending their homies in lockdown birthday cards, complete with elaborately coded gang symbolism. The cards are often intercepted by prison authorities, who rely on them as a source of intelligence about inmates' gang loyalties:
On the front of the homemade greeting was a cartoon of a gangster holding a MAC-10 automatic pistol. The card was bordered in blue, the Crips' signature color. And because Crips avoid the letter "B" at all costs -- due to its association with their rival gang, the Bloods -- the card happily announced "Happy C-Day."
"That's where you get a lot of your information, from these birthday cards," said Officer Steve Preciado, a Lancaster gang investigator. "A lot of times their family members won't send them nothing. But the gangsters will put their nicknames on these cards, and where they're from, like 'Shorty from Pacoima.' So your job is to find out who Shorty is."
(via bOING bOING)
2004/4/6
A picture is emerging of the Madrid bombers (most of whom are believed to have killed themselves with a bomb when besieged); and it appears that they gave no clue to being Islamic fundamentalists:
Neighbours who lived near Fakhet, and many of the other suspects, had little reason to think that they were militants with a fundamentalist agenda. Many of them appeared westernised and integrated into the Spanish community, with a liking for football, fashion, drinking and Spanish girlfriends, say Spanish press reports.
Ahmidan is also said to have seemed happily integrated in Spanish society, whose Spanish friends are said to have included women who sported crop tops, tattoos and piercings.
Which is a sobering thought; the "brigades of death" could be among us, not merely keeping quietly to themselves whilst catching your bus or working in your office, but popping Es at your favourite nightclub, barracking for your footy team, and discussing the finer points of your favourite reality-TV show with you over a beer; right up until the end when they cast off the façade of their normal life and kill you and your loved ones.
Either that or the right-wing talk radio jocks are right and people with tattoos, piercings and countercultural leanings are in league with the terrorists.
2004/4/2
The BBC has an thread, inviting readers to recount their favourite April Fools' jokes, and other miscellany, such as this almost Zen story:
Many many years ago, my cousin, a gullible young Factory Apprentice, was sent off to a distant corner of the plant, having been told to "ask old Joe for a long weight". Of course, Joe said "Hang on here, while I go and get it". Some two hours later, Joe returns, empty handed, cousin asks him where the long weight is. "You've just had it, mate".... (John, England)
Along similar lines, a list of online April Fools jokes, and the Top 100 April Fool's Hoaxes of All Time (a rerun, but a good one).
2003/11/13
Scientists are discovering the neurological bases of social phenomena such as romantic love, trust, self-awareness and deception.
"We believe romantic love is a developed form of one of three primary brain networks that evolved to direct mammalian reproduction," says researcher Helen Fisher, PhD, of Rutgers University in New Brunswick, NJ. "The sex drive evolved to motivate individuals to seek sex with any appropriate partner. Attraction, the mammalian precursor of romantic love, evolved to enable individuals to pursue preferred mating partners, thereby conserving courtship time and energy. The brain circuitry for male-female attachment evolved to enable individuals to remain with a mate long enough to complete species-specific parenting duties."
In the new research, Zak and his colleagues find that when someone observes that another person trusts them, oxytocin - a hormone that circulates in the brain and the body - rises. The stronger the signal of trust, the more oxytocin increases. In addition, the more oxytocin increases, the more trustworthy (reciprocating trust) people are.
"Interestingly, participants in this experiment were unable to articulate why they behaved they way they did, but nonetheless their brains guided them to behave in `socially desirable ways,' that is, to be trustworthy," says Zak. "This tells us that human beings are exquisitely attuned to interpreting and responding to social signals.
(Or, perhaps, that what we know as the conscious mind doesn't so much make decisions or control our behaviour as rationalise it; could it be that the conscious mind does little more than provide a running commentary for the many physical processes happening in the brain and nervous system, and the (advantageous) illusion of a coherent, unified "self"? But I digress.)
And in other related news: a wink sends testosterone soaring:
He paid male students $10 to come into the lab and leave a saliva sample. Unbeknownst to the men, the scientists staged a five-minute chat with a twentysomething female research assistant before they spit. This brief brush set the men's hormones surging: testosterone levels in their spit shot up around 30%. The higher a man's hormone soared, the more the female research assistant judged that he was out to impress - by talking about himself, for example.
2003/8/13
Looking for something to spend your millions on and alleviate your ennui? Try secretly raising a second family under an assumed name, like Douglas Cone of Tampa, Florida did for some 30 years.
2003/6/27
An Independent piece claiming similarities between Tony Blair and Mussolini:
For a start, Blair extols the virtues of the Third Way, which was the phrase coined by the Fascists, no less, to describe their alternative to capitalism and communism. Blair began as a left-wing pacifist and became a right-wing warmonger. He is dictatorial and ignores Parliament if he can and he is a master of propaganda (spin). He is also a bit of a musician - always a dangerous sign in a politician - and plays the electric guitar. So was Mussolini. He played the violin.
People, especially people on the left, tend to forget - presumably because it is inconvenient to remember - that Mussolini was a revolutionary socialist before he was anything else. They forget, too, that he founded Fascism not as a right-wing dictatorship but as a left-wing revolutionary movement that provided an alternative first to socialism then to communism.
It then goes on to compare Mussolini's Corporate State with the New Labour Third Way of corporatisation and neo-liberal economics. And then there's both statesmen's gift for spin:
A phrase Mussolini often used to describe the Italian parliament was that it was "invincibly nauseous". Fascism transformed political participation from an isolated act involving the ballot box into a daily act of religious faith. Blair has not - heavens, no - abolished democracy as Mussolini did, but democracy has diminished under Blair. The Opposition languishes in torpid impotence. The Prime Minister appears increasingly to resemble some whacky kind of cult leader. He avoids debate in Parliament if he can. He talks to the people direct, via television, as Mussolini did via the piazza. Mussolini was famous for his balcony speeches - his "dialogues with the crowd". A modern Mussolini would not need to do anything so obvious as to tackle democracy head on. He could just side-step it with spin.
(via FmH)
2003/6/10
The latest tool for the modern pick-up artist: fake ATM receipts with unfeasibly large balances written on them. Next time you meet an attractive gold-digger type in a dive bar, jot your number down on one of them (which you happened to have in your pocket; note: don't pull out a pristine new roll of them or you'll blow your cover), and when she (or he) sees "your" balance, they'll call you back straight away. Though if you're going to do that, why not print your own? (via MeFi)
2003/4/8
Blogs can save lives. For example, feedback from helpful readers can tell you if the amazingly cool new girlfriend you just posted about is, in fact, a sociopathic compulsive liar with a long history of screwing people over.
Then Whistleblower followed with a series of identity theft stories. New Girl would steal online photos of various gothgirls and claim to be them in various chat rooms, chatting up gothguys and in some cases convincing them to fly up to meet her. One poor guy came incredibly close to doing so until the person whom she was posing as managed to warn him.
("Gothgirls"? "Gothguys"? Here's clue #1...)
[someone else] then told me about how she and New Girl met, at rehab meetings. Rehab?! And later, since New Girl had no place to stay, she let her stay on her couch. They grew closer and became lovers. Lovers?! And then came the story about how New Girl tried to hide her pregnancy. Pregnancy?!
(via bOING bOING)
2003/2/9
More on Tony "the Smiler" Blair's plagiarised "smoking gun" report on Iraq. Apparently Nu Labour spin doctor Alastair Campbell, the man who gave us "Cool Brittannia", was behind it. Blair's image has suffered since, as it has become blindingly obvious that the man has the integrity of a used-car salesman.
2003/1/14
Via FmH, two more paranoid than usual links; firstly a guide on how to disappear in America without a trace, much of which is probably quaintly anachronistic. Though the gist is, if they really want to find you, they will, no matter what you do.
Satellites can bounce LASER light off of your windows and, by measuring the minute distance differences between a vibrating window and the satellite, reconstruct your speech -- from orbit! I don't know how much this process costs yet it was demonstrated for PBS some years ago so it may not be all that expensive. The quality of the audio is poor but it can be understood.
Given Moore's Law and the dropping costs of high technology, it's not all that far-fetched to imagine that this sort of thing is now being used on deadbeat dads and people with overdue library books; or if it isn't, will be soon.
Secondly, a somewhat more academic and less Loompanicsesque paper on surveillance techniques and countermeasures, with a catalogue of 11 types of strategies against surveillance:
A common form of switching involves certification transference: A ticket, entry card, license, entitlement or identity marker belonging to someone else is used. South Africa provides an unusual example. There, welfare payments can be obtained from ATM machines. The recipient enters the correct information into the computer and offers a thumb print for verification. A colleague reported one enterprising family that collected welfare payments long after an elderly relative had died. They cut off her thumb and continued to use it.
A more subtle form involves conversational ploys in which a surveillance agent is duped into believing that a machine is invalid. Consider the story told me by a Russian. A family coming back from a picnic is stopped by police and the driver fails a breathalyzer test. He protests, "That's impossible, I haven't been drinking, your machine must be broken. Please try it on my wife." She also fails the test. The man gets even more insistent that the machine is broken and says, "Please try it on my young daughter." She is tested and also fails. At which point the police officer, doubting his own machine, lets the man go. The man later remarks to his wife, "That was really a good idea to let her drink with us.
Writing in invisible ink is a familiar children's game and it has its' adult counterparts, although these may rely on bad science. Thus, a bank robber was identified and arrested in spite of rubbing lemon juice on his face because he had been told that it would prevent the surveillance camera from creating a clear picture.
(Of course, these links are provided for the curiosity and interest of law-abiding readers only. If you're an al-Qaeda terrorist, drug user, MP3 pirate or other criminal, please do not follow them. We thank you for your cooperation.)
2002/12/29
What is it about trains and public transport that attracts the unhinged? A 21-year-old New York man was arrested for impersonating a Subway motorman -- for the 16th time. Edward Brown, described as a "transit buff", wore a stolen uniform and hung around in subway employee lounges chatting with employees; he says he won't stop doing so until the Transit Authority hires him. (via rotten.com)
2002/8/2
Frustrated with CityLink toll evaders speeding through their residential streets every day, some Melbourne suburbanites are fighting back, by staking out the streets with hairdryers, pretending they're radar guns. Wonder how long until the two-wheels-good-four-wheels-bad crowd take this up as a form of direct action.
2002/8/1
The next wave in marketing is here: chatroom bots or "buddies" with virtual personalities, which befriend people, make conversation and gently encourage them to consume lifestyle products -- and potentially provide marketing analysts with a lot of customer-profile data in the form of conversations.
Most buddies are programmed with personalities that appeal to their target audiences. ELLEgirlBuddy, the Internet ego of teen magazine ELLEgirl, is a redheaded 16-year-old who likes kickboxing, the color periwinkle and French class. GooglyMinotaur, a buddy for the British progressive rock band Radiohead, affected a British demeanor with words like "mate." The Austin Powers buddy, which promotes the summer film "Goldmember," interjects the movie character's favorite phrases - "yeah, baby" and "grrr" - into conversation.
Perhaps surprisingly, thanks to improvements in natural-language technology and extensive customer databases, the bots give the illusion of being sentient. People know they're machines, but choose to suspend disbelief.
ActiveBuddy's bots save details about each user - names, birth dates, even instances when the person used offensive language. When the buddy recalls these facts, it could appear to the user that it is taking a genuine interest in him or her. "We're programmed to respond to certain signals as though in the presence of a life form," said MIT's Turkle. "These objects are pushing our buttons."
(via TechDirt)
2001/9/16
The WTC attack: Intelligence consultancy Stratfor believes that clues left behind by the terrorists were red herrings, designed to throw investigators off the trail and buy them time.
The attackers knew how to avoid detection by the National Security Agency and other technical intelligence outfits while organizing outside the United States. They also knew how to avoid suspicion once in the United States. That means they had a sophisticated understanding of how U.S. intelligence works and the discipline to avoid triggering suspicion. It is nearly unbelievable that an organization capable of carrying out such a complex operation would leave behind relatively obvious evidence.
There are also unconfirmed reports that pictures of Saudi dissident Osama bin Laden, widely viewed as a prime suspect in the attacks, and copies of the Quran were left in rental vehicles used by the suspects. For intelligence operatives who earlier exhibited remarkable skill, such theatrics do not make sense.
I thought that the car full of Arabic-language flight manuals seemed a bit too obvious.
2001/8/18
The future of online marketing? As banner-ad revenue declines and online marketers search for new ways to irritate their customers into paying attention, an English magazine firm has come across an attention-grabbing new tactic: Emap send email to customers, accusing them of accessing illegal pornography, telling them that details had been passed on to the police, and offering a link they could click to appeal against the charges. The link went to a web site advertising the MaxPower car show, orgainsed by Emap. What next? "I've been screwing your wife. Click here to see my AIDS test results.", perhaps? (via Found)
2000/6/23
The technology for electronically faking video footage is coming to fruition. And we all know how the street finds its own uses for new technologies...
A demo tape supplied by PVI bolsters the point in the prosaic setting of a suburban parking lot. The scene appears ordinary except for a disturbing feature: Amidst the SUVs and minivans are several parked tanks and one armored behemoth rolling incongruously along. Imagine a tape of virtual Pakistani tanks rolling over the border into India pitched to news outlets as authentic, and you get a feel for the kind of trouble that deceptive imagery could stir up.
Suddenly those large stretches of programming between commercials-the actual show, that is-become available for billions of dollars worth of primetime advertising. PVI's demo tape, for instance, includes a scene in which a Microsoft Windows box appears-virtually, of course-on the shelf of Frasier Crane's studio. This kind of product placement could become more and more important as new video recording technologies such as TiVo and RePlayTV give viewers more power to edit out commercials.
With just a few minutes of video of someone talking, their system captures and stores a set of video snapshots of the way that a person's mouth-area looks and moves when saying different sets of sounds. Drawing from the resulting library of "visemes" makes it possible to depict the person seeming to say anything the producers dream up-including utterances that the subject wouldn't be caught dead saying. In one test application, computer scientist Christoph Bregler, now of Stanford University, and colleagues digitized two minutes of public-domain footage of President John F. Kennedy speaking during the Cuban missile crisis in 1962. Using the resulting viseme library, the researchers created "animations" of Kennedy's mouth saying things he never said, among them, "I never met Forrest Gump."
1999/8/16
Interesting article on salon.com, listing some choice entries in a practical memetic engineering contest:
How does the author of a computer virus get the unsuspecting victim to open the attachment? We invited readers to create irresistible virus wrappers. Here, we've collected some of the more devious and effective submissions."Dear Lucky Winner,
You've been selected to participate in our first-ever E-mail Sweepstakes! Double-click on the enclosed electronic registration form -- everyone wins at least $500!"