The Null Device
Posts matching tags 'malware'
2010/8/20
Two years ago, a Spanish airliner crashed shortly after takeoff from Madrid, killing 154 passengers. Now, a Spanish news article (machine-translated here) claims that the crash may have been due to an aircraft maintenance computer having been infected with malware and failing to flag two faults which, had they been noticed, would have resulted in the plane having been taken out of service. If this is true, would it be the highest body count of any computer virus so far?
2010/4/15
The War on Copyright Piracy has many uses: in Kyrgyzstan, for example, the government is using the pretext of anti-piracy raids to shut down opposition media, by having goons with alleged Microsoft affiliations seize computers:
Stan TV employees told CPJ that police were accompanied by a technical expert, Sergey Pavlovsky, who claimed to be a representative of Microsoft’s Bishkek office. According to the journalists, Pavlovsky said he had authorization papers from Microsoft but was unwilling to show them. After a cursory inspection of the computers, they said, Pavlovsky declared all of the equipment to be using pirated software. Stan TV’s work computers, as well as the personal laptops of journalists, were seized; the offices were also sealed, interrupting the station’s work.Microsoft have disowned any connection to the raid.
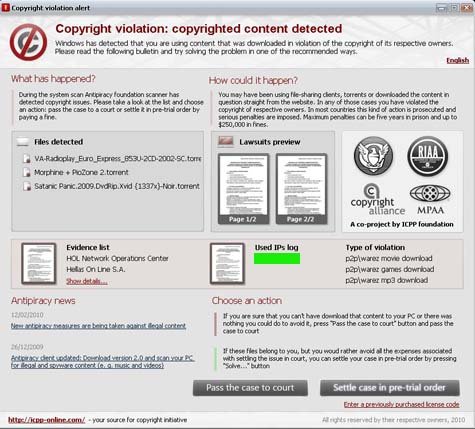
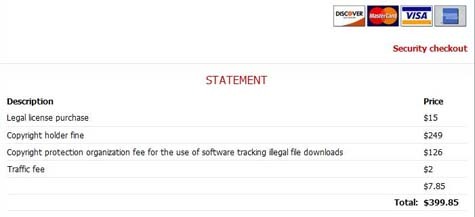
Meanwhile, enterprising malware entrepreneurs have jumped onto the copyright lawsuit bandwagon; a new piece of malware for Windows scans users' hard drives for torrents, and threatens the users with lawsuits, demanding payment by credit card:
(via Boing Boing, Download Squad) ¶ 0
2009/1/14
An interesting interview with a former Windows adware author, by all accounts a very smart guy (albeit of, shall we say, above-average ethical flexibility), exposing both the security exploits used by Windows malware, the arms races in the malware underground and the dodgy business models of the industry:
The good distributors would say, ‘This is ad-supported software.” Not-so-good distributors actually did distribute through Windows exploits. Also, some adware distributors would sell access. In their licensing terms, the EULA people agree to, they would say “in addition, we get to install any other software we feel like putting on.” Of course, nobody reads EULAs, so a lot of people agreed to that. If they had, say, 4 million machines, which was a pretty good sized adware network, they would just go up to every other adware distributor and say “Hey! I’ve got 4 million machines. Do you want to pay 20 cents a machine? I’ll put you on all of them.” At the time there was basically no law around this. EULAs were recognized as contracts and all, so that’s pretty much how distribution happened.
So we’ve progressed now from having just a Registry key entry, to having an executable, to having a randomly-named executable, to having an executable which is shuffled around a little bit on each machine, to one that’s encrypted– really more just obfuscated– to an executable that doesn’t even run as an executable. It runs merely as a series of threads. Now, those threads can communicate with one another, they would check to make sure that the BHO was there and up, and that the whatever other software we had was also up.
There was one further step that we were going to take but didn’t end up doing, and that is we were going to get rid of threads entirely, and just use interrupt handlers. It turns out that in Windows, you can get access to the interrupt handler pretty easily. In fact, you can register with the OS a chunk of code to handle a given interrupt. Then all you have to do is arrange for an interrupt to happen, and every time that interrupt happens, you wake up, do your stuff and go away. We never got to actually do that, but it was something we were thinking we’d do.He also talks about making his registry entries unremovable by using obscure Unicode APIs to add them and putting in characters illegal to the ASCII-based APIs most of Windows uses (oops!), writing device drivers to further pwn the hapless users' machines, and also deploying more Scheme runtime than probably anyone else:
There was also of course Scheme. Eventually, we got sick of writing a new C program every time we wanted to go kick somebody off of a machine. Everybody said, “What we need is something configurable.” I said, “Let’s install a Turing-complete language,” and for that I used tinyScheme, which is a BSD licensed, very small, very fast implementation of Scheme that can be compiled down into about a 20K executable if you know what you’re doing.
Eventually, instead of writing individual executables every time a worm came out, I would just write some Scheme code, put that up on the server, and then immediately all sorts of things would go dark. It amounted to a distributed code war on a 4-10 million-node network.So not only is a botnet of pwned Windows PCs likely to be the world's most powerful supercomputer (in purely numerical terms, at least), but a network of dodgy adware could well have been the peak of Scheme's deployment in the real world.
The author's advice to anyone wanting to avoid adware is "um, run UNIX".
2008/4/3
Apparently 2% of internet traffic now consists of denial-of-service attacks, mostly launched by botnets of hijacked Windows PCs operated remotely by organised crime. By comparison, email comprises 1 to 1.5% of internet traffic (though a majority of that is reportedly spam).
2008/3/27
Someone is sending pro-Tibet groups documents infected with keylogging malware, configured to send back keystrokes to a server in China. The documents are sent from addresses forged to resemble human rights groups, and purport to be details of Chinese massacres in Tibet and similar information.
The exploit silently drops and runs a file called C:\Program Files\Update\winkey.exe. This is a keylogger that collects and sends everything typed on the affected machine to a server running at xsz.8800.org. And 8800.org is a Chinese DNS-bouncer system that, while not rogue by itself, has been used over and over again in various targeted attacks.
The exploit inside the PDF file was crafted to evade detection by most antivirus products at the time it was sent.
Somebody is trying to use pro-Tibet themed emails to infect computers of the members of pro-Tibet groups to spy on their actions.Of course, the pro-Tibet groups could avoid being pwn3d by the Chinese by the simple expedient of not using Windows or common software to open documents.
2008/1/27
Details have emerged of how the Bavarian police intercept Skype calls and encrypted internet traffic. Apparently they use specially written malware, from a company named Digitask. The malware needs to be installed on the suspect's computer (which can be done in a number of ways; if they can't get a black-bag team in, they can send an email carrying the trojan. Looks like Bavaria's safe from criminals who use Windows then.
2007/4/25
Computer criminals have found a new way of distributing bank-account-stealing trojans: by scattering USB flash drives in car parks. Some percentage of the population (perhaps the same that opens email attachments) would pick up these shiny flash disks, take them home and insert them into their Windows PCs, not having disabled autorunning beforehand.
Sooner or later, the default Windows configuration will refuse to autorun content on a strange flash drive, and this won't work. Unless, of course, the criminals have special USB units manufactured containing an active processor which uses DMA to probe and interfere with the host PC's memory. They could possibly use the same facilities they use to make fake ATM front panels to manufacture them. The units could even contain an empty, perfectly innocent flash drive to deflect suspicion; after all, there's no limit to how many devices something on the end of a USB connector can appear to be.
2005/12/7
The latest advance in Windows worms is a worm which takes over people's instant-messaging accounts and chats to their friends, attempting to talk them into downloading it; in short, an automated form of social engineering:
According to IMlogic, the worm, dubbed IM.Myspace04.AIM, has arrived in instant messages that state: "lol thats cool" and included a URL to a malicious file "clarissa17.pif." When unsuspecting users have responded, perhaps asking if the attachment contained a virus, the worm has replied: "lol no its not its a virus", IMlogic said.Which suggests that the Turing test may be easier to pass in an environment where people start messages with "lol". If your friends suddenly turn into giggling prepubescents and start trying to convince you to download a file, you know what's happening.
I wonder whether this will lead to an arms race in worm conversational abilities. Perhaps the next one will trawl message logs and pick out phrases/words used by that contact (or use them to change its own writing style)?
2005/11/25
Scare meme of the day: if bird flu, al-Qaeda weaponised ebola or a meteor strike don't get us, alien computer viruses exploiting Seti@Home to take over Earth's computer systems just might. Assuming, of course, that the aliens understand enough about our puny earthling computer architectures, operating systems and library vulnerabilities to write a useful exploit and encode it the right way in a radio signal.
(via bOING bOING) ¶ 0
2005/11/1
Another reason to avoid "Copy Controlled"/"Copy Protected" CDs: some of them (at least the ones from Sony BMG) install rootkits on your Windows PC; ones which, if an attempt is made to remove them, disable your CD-ROM drive. Someone at Sony BMG should go to jail for this, though probably won't.
(via ![]() substitute) ¶ 0
substitute) ¶ 0
2005/5/30
The latest malware won't merely spew ads at you or use your Windows PC as a zombie to send spam: it will encrypt your files and demand a ransom for the key:
Stewart managed to unlock the infected computer files without paying the extortion, but he worries that improved versions might be more difficult to overcome. Internet attacks commonly become more effective as they evolve over time as hackers learn to avoid the mistakes of earlier infections.
"The problem is getting away with it -- you've got to send the money somewhere," Stewart said. "If it involves some sort of monetary transaction, it's far easier to trace than an e-mail account."Perhaps future versions will demand that the users donate CPU cycles/network bandwidth instead of money? Then again, those are easy enough to steal without extortion.
2004/12/30
Thanks to the technological miracle of Microsoft DRM, Windows Media files can contain adware, viruses and spyware, and it appears that an anti-P2P company named Overpeer have been launching such trojan WMAs into the KaZaA network. More details here:
But since the license dialog box acts just like an Internet Explorer window, it can display whatever is on the page it points to--whether a legitimate call for license information or a series of pop-up ads.
Not only did we get bombarded with unwanted ads, but one of the ad windows in a video file tried to install adware onto our test PC surreptitiously, while another added items to our browser's Favorites list and attempted to change our home page. And a window from the original music file asked to download a file called lyrics.zip, which contained the installer for 180search Assistant, commonly categorized as an adware program.
And if the asphead agencies can do it, so can the Bulgarian Mafia and their ilk. Expect to see spam-zombie-trojan-infected WMAs appearing on a file-sharing network near you. The moral of this story, kids, is use MP3 don't pirate music.
(via bOING bOING)
2004/5/27
An economic-rationalist arguments for why writing computer viruses should be punishable by death; it basically comes down to society getting more economic benefits from executing worm writers than from killing murderers. It reminds me a bit of the argument in K.W. Jeter's Noir about why copyright violation had to become punishable by death, and worse. (via Techdirt)
2004/2/17
The rather eye-opening dissection of an online greeting-card spam; an email telling the user to go to a web site to see an electronic greeting card, and the website in question, which uses Internet Explorer security holes to overwrite your Windows Media Player and install a keylogger apparently programmed to look for online banking sites (and undetectable by current spyware detectors). Nasty; and another reason to not use IE (or, preferably, Windows). (via Slashdot)
2003/12/19
The PCs at a certain hostel in Byron Bay appear to be fuzzy with adware; every few minutes, a program named "Save!" throws up a pop-under ad for some product. Not sure whether they installed it themselves or whether it snuck in with a "funny screensaver" or porn downloader or something.
"Save!", which claims to be associated with some outfit named "WhenU", strenuously disclaims acting as spyware, logging websites, passwords or anything like that. Though, of course, any piece of conspicuous spyware would say that as well. Just in case, I've taken to entering passwords by cutting and pasting words from other pages, deleting bits of them and adding the odd keystroke or two. It is probably theoretically possible to write a piece of spyware that keeps track of pastes, cursor positions, &c. into a password entry box, but in practice it may be quite difficult.
I wonder whether the alleged yuppification of Byron Bay has extended to there being wireless internet anywhere.
2003/3/19
Quelle surprise:
Those "Copy Controlled" CDs EMI have been foisting on the public
aren't proving very popular. Apparently, they don't play in some car stereos, and the top-s3krit Windows software that auto-installs when you try to play the CD may do things to your registry without your consent. EMI, of course, won't tell you what it does because it's a secret and if people find out how it works, then the terrorists pirates will have won. I've heard of people successfully ripping them on Windows and/or Linux, though they may have been mislabelled clear CDs (given that no software automatically started).
I wonder how long until recorded music comes with a shrink-wrap license prohibiting you from circumventing copy-denial mechanisms or making unencrypted MP3s of it, and indemnifying the company for any changes made to your system software?
(I can't see EMI's security-through-obscurity scheme holding up for very long, especially since it doesn't rely on "trusted client" PCs or anything. Soon enough, some guy without a girlfriend will break it and upload the details to a server somewhere. Yes, he may go to jail for it, but that hasn't stopped virus writers.)
2003/1/31
Another part of the Windows web browsing experience us Linux users miss out on: Malignant toolbar installs itself into Internet Exploiter, redirects home page/web searches to xupiter.com (owned by a shadowy Hungarian company, apparently) or the sites of businesses who paid them for placement (and who are, I would guess, unlikely to be highly ethical), and downloads pop-up gambling games behind your back. The toolbar resists attempts at uninstallation, and the programmers keep changing its code to keep one step ahead of anti-spyware tools.
Healan said some installations probably occurred when people clicked "OK" in a pop-up box without really knowing what they had agreed to, or when they meant to close the pop-up window.
2002/9/27
First there was spyware, and now there's diversionware; hidden add-ons to free Windows utilities/toys, which intercept the user's web requests to shopping web sites and substitute in the software maker's affiliate ID, even if someone else's ID was used. And this is completely legal, because users agree to it in the click-through licence agreements.
I suppose that's a key cultural distinction between UNIX and Windows. In the UNIX world, "free software" implies Richard Stallman's ideology. In the Windows world, "free software" implies layers of parasitic spyware and diversionware working behind the user's back. (via Techdirt)
2002/5/8
Extreme marketing in the new millennium: Here come the banner ads which install spyware, disable firewall software; the rogue pop-up ad in question uses a Shockwave applet and an Internet Explorer bug to surreptitiously download and install the software onto the user's PC. Needless to say, it only affects the 99.999% of users who use Windows; Maccies and Penguinheads can look smug.
1999/10/16
Viral marketing: Windows email worm links to porn sites, sends itself to victim's contacts. (CNN)