The Null Device
Posts matching tags 'nsa'
2014/2/11
As the Snowden revelations have demonstrated that we do, in fact, live in a very discreet surveillance dystopia, it can be tempting to ask, what's the problem? After all, the security services don't seem to be actually running COINTELPRO-style operations against Occupy activists or disappearing dissidents at 3AM, and the thunderbolts from Olympus (this side of Afghanistan, at least) seem to be limited to DDOS operations against script kiddies (live by the sword, die by the sword, as they day) and the occasional drug-enforcement agent getting very lucky when performing a "random" search (which, whilst it goes against peacetime luxuries such as due process, doesn't affect law-abiding bourgeoisie like you and me, right?) If you've got nothing to hide (or just the usual minor indiscretions that the spooks don't care about), you've got nothing to fear, and all those people deterred from associating with pacifist churches and human-rights groups can only be a bunch of nervous nellies jumping at shadows, given that not only the NSA but Facebook and Google know exactly what political leanings they have. After all, the more data the spooks have on everyone, surely that would make it easier for them to sort the signal from the noise; to tell, for example, that while you may have and made a phone call referring to a movie as a "bomb" whilst within range the same cell tower as two anarchists and a Wahhabi Muslim, you don't look like a terrorist, right?
The only problem is it doesn't work that way, as the case of Brandon Mayfield demonstrates:
But there’s another danger that Snowden didn’t mention that’s inherent in the government’s having easy access to the voluminous data we produce every day: It can imply guilt where there is none. When investigators have mountains of data on a particular target, it’s easy to see only the data points that confirm their theories — especially in counterterrorism investigations when the stakes are so high — while ignoring or downplaying the rest. There doesn’t have to be any particular malice on the part of investigators or analysts, although prejudice no doubt comes into play, just circumstantial evidence and the dangerous belief in their intuition. Social scientists refer to this phenomenon as confirmation bias, and when people are confronted with data overload, it’s much easier to weave the data into a narrative that substantiates what they already believe. Criminologist D. Kim Rossmo, a retired detective inspector of the Vancouver Police Department, was so concerned about confirmation bias and the investigative failures it causes that he warned police officers in Police Chief magazine to always be on guard against it. “The components of confirmation bias,” he wrote, “include failure to seek evidence that would disprove the theory, not utilizing such evidence if found, refusing to consider alternative hypotheses and not evaluating evidence diagnosticity.”
Despite finding that Mayfield’s print was not an identical match to the print left on the bag of detonators, FBI fingerprint examiners rationalized away the differences, according to a report by the Department of Justice’s Office of the Inspector General (OIG). Under the one discrepancy rule, the FBI lab should have concluded Mayfield did not leave the print found in Madrid — a conclusion the SNP reached and repeatedly communicated to the FBI. The FBI’s Portland field office, however, used that fingerprint match to begin digging into Mayfield’s background. Certain details of the attorney’s life convinced the agents that they had their man. Mayfield had converted to Islam after meeting his wife, an Egyptian. He had represented one of the Portland Seven, a group of men who tried to travel to Afghanistan to fight for al Qaeda and the Taliban against U.S. and coalition forces in a child custody case. He also worshipped at the same mosque as the militants. In the aftermath of 9/11, these innocent associations and relationships, however tangential, were transformed by investigators into evidence that Mayfield wasn’t a civic-minded American, but a bloodthirsty terrorist intent on destroying the West.
FBI agents broke into Mayfield’s home and law office. They rifled through documents protected by attorney-client privilege, wiretapped his phones, analyzed his financial records and web browsing history, and went through his garbage. They followed him wherever he went. Despite all this, the FBI never found a smoking gun connecting him to Madrid. They did, however, find Internet searches of flights to Spain and learned that he once took flying lessons. To FBI agents already convinced of his guilt, this was all evidence of Mayfield’s terrorist heart. The Web searches, however, were mundane. His daughter had to plan a fictional vacation for a school project. Flight lessons were indicative of nothing more than Mayfield’s interest in flying.
2013/9/18
Builders of Star Trek-inspired rooms recently in the news: a convicted paedophile (or, to be precise, another one, though his Star Trek-inspired flat has been in the news previously), and the US National Security Agency.
2013/8/20
A few days ago, David Miranda, a Brazilian man who is the partner of investigative journalist Glenn Greenwald, was detained for nine hours under anti-terrorism legislation whilst passing through Heathrow on the way from Berlin to his home in Brazil. Metropolitan Police threatened him with imprisonment, demanded his passwords and seized all electronic devices on his person; GCHQ have been unable to crack encrypted files seized from him, which could be plans for a doomsday device. Or they might not.
US conservative columnist Andrew Sullivan has compared this incident to events in Putin's Russia:
In this respect, I can say this to David Cameron. Thank you for clearing the air on these matters of surveillance. You have now demonstrated beyond any reasonable doubt that these anti-terror provisions are capable of rank abuse. Unless some other facts emerge, there is really no difference in kind between you and Vladimir Putin. You have used police powers granted for anti-terrorism and deployed them to target and intimidate journalists deemed enemies of the state.
You have proven that these laws can be hideously abused. Which means they must be repealed. You have broken the trust that enables any such legislation to survive in a democracy. By so doing, you have attacked British democracy itself. What on earth do you have to say for yourself? And were you, in any way, encouraged by the US administration to do such a thing?The Whitehouse "says" "it" "played" "no" "role" "in" the detention, though acknowledged that it was briefed on Miranda's presence on the plane and on the detention, as was PM David Cameron. Which suggests that, unless one makes the extraordinary mental gymnastics of extending the definition of “terrorism” to leaking information embarrassing national security agencies, this was a naked act of intimidation against a journalist by targeting his family, of the sort practiced in China and Iran.
Meanwhile, it emerged that, a month earlier, officers of the security services raided the headquarters of the Guardian and forced staff to destroy hard drives and computers used to store the NSA revelations. Copies apparently exist abroad, for the time being, with Guardian staff working on the case being based in the New York office.
I wonder how long until the Guardian relocates its editorial headquarters to a location that is not a pervasive security state, selling the shiny new building they have at Kings Place (though perhaps keeping a floor as a local bureau and/or for writing whimsical middle-class humour columns for the Saturday supplement) and using part of the undoubtedly hefty profit to buy a block in, say, downtown Reykjavík?
Also, Groklaw founder Pamela Jones has shut the site down, on account of the environment of pervasive surveillance, and is going into internal exile off the internet:
One function of privacy is to provide a safe space away from terror or other assaultive experiences. When you remove a person's ability to sequester herself, or intimate information about herself, you make her extremely vulnerable....
The totalitarian state watches everyone, but keeps its own plans secret. Privacy is seen as dangerous because it enhances resistance. Constantly spying and then confronting people with what are often petty transgressions is a way of maintaining social control and unnerving and disempowering opposition....
And even when one shakes real pursuers, it is often hard to rid oneself of the feeling of being watched -- which is why surveillance is an extremely powerful way to control people. The mind's tendency to still feel observed when alone... can be inhibiting. ... Feeling watched, but not knowing for sure, nor knowing if, when, or how the hostile surveyor may strike, people often become fearful, constricted, and distracted.
My personal decision is to get off of the Internet to the degree it's possible. I'm just an ordinary person. But I really know, after all my research and some serious thinking things through, that I can't stay online personally without losing my humanness, now that I know that ensuring privacy online is impossible. I find myself unable to write. I've always been a private person. That's why I never wanted to be a celebrity and why I fought hard to maintain both my privacy and yours.And here's Charlie Stross' take, in which he connects the British security state to David Cameron's mandatory anti-porn internet filter plans:
The spooks are not stupid. There are two ways they can respond to this in a manner consistent with their current objectives. They can try to shut down the press — a distinct possibility within the UK, but still incredibly dangerous — or they can shut down the open internet, in order to stop the information leakage over that channel and, more ambitiously, to stop the public reading undesirable news.I think they're going for the latter option, although I doubt they can make it stick. Let me walk you through the early stages of what I think is going to happen.
If you can tap data from the major search engines, how hard is it to insert search results into their output? Easy, it turns out. As easy as falling off a log. Google and Facebook are both advertising businesses. Twitter's trying to become one. Amazon and Ebay both rent space at the top of their search results to vendors who pay more money or offer more profits. Advertising is the keyword. All the NSA needs, in addition to the current information gathering capability, is the ability to inject spurious search results that submerge whatever nugget the user might be hunting for in a sea of irrelevant sewage. Imagine hunting for "Snowden" on Google and, instead of finding The New York Times or The Guardian's in-depth coverage, finding page after page of links to spam blogs.
2013/8/4
Bruce Sterling has written a witty and insightful essay about the NSA leaks and the Edward Snowden situation:
This is the kind of comedic situation that Russians find hilarious. I mean, sure it’s plenty bad and all that, PRISM, XKeyScore, show trials, surveillance, threats to what’s left of journalism, sure, I get all that, I’m properly concerned. None of that stops it from being hilarious.
Modern Russia is run entirely by spies. It’s class rule by the “siloviki,” it’s Putin’s “managed democracy.” That’s the end game for civil society when elections mean little or nothing, and intelligence services own the media, and also the oil. And that’s groovy, sure, it’s working out for them.
Citizens and rights have nothing to do with elite, covert technologies! The targets of surveillance are oblivious dorks, they’re not even newbies! Even US Senators are decorative objects for the NSA. An American Senator knows as much about PRISM and XKeyScore as a troll-doll on the dashboard knows about internal combustion.
If you’re a typical NSA geek, and you stare in all due horror at Julian, it’s impossible not to recognize him as one of your own breed. He’s got the math fixation, the stilted speech, the thousand-yard-stare, and even the private idiolect that somehow allows NSA guys to make up their own vocabulary whenever addressing Congress (who don’t matter) and haranguing black-hat hacker security conventions (who obviously do).
The civil lib contingent here looks, if anything, even stupider than the US Senate Intelligence Oversight contingent — who have at least been paying lavishly to fund the NSA, and to invent a pet surveillance court for it, with secret laws. That silly Potemkin mechanism — it’s like a cardboard steering wheel in the cockpit of a Predator drone.
And, yeah, by the way, Microsoft, Apple, Cisco, Google et al, they are all the blood brothers of Huawei in China — because they are intelligence assets posing as commercial operations. They are surveillance marketers. They give you free stuff in order to spy on you and pass that info along the value chain. Personal computers can have users, but social media has livestock.
So, the truth is out there, but nobody’s gonna clean up all that falsehood. There is no visible way to make a clean break with the gigantic, ongoing institutional deceits. There’s no mechanism by which any such honesty could be imposed. It’s like reforming polygamy in the Ottoman Empire.
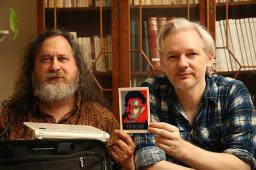
People, you couldn’t trust any of these three guys to go down to the corner grocery for a pack of cigarettes. Stallman would bring you tiny peat-pots of baby tobacco plants, then tell you to grow your own. Assange would buy the cigarettes, but smoke them all himself while coding up something unworkable. And Ed would set fire to himself, to prove to an innocent mankind that tobacco is a monstrous and cancerous evil that must be exposed at all costs.
2013/6/9
One reaction to the revelations about the NSA's surveillance programmes has been along the lines of the old chestnut that “if you have nothing to hide, you have nothing to fear”. One commenter, who claims to have lived under a Middle Eastern dictatorship, debunks this:
1) the purpose of this surveillance from the governments point of view is to control enemies of the state. Not terrorists. People who are coalescing around ideas that would destabilize the status quo. These could be religious ideas. These could be groups like anon who are too good with tech for the governments liking. It makes it very easy to know who these people are. It also makes it very simple to control these people.
Lets say you are a college student and you get in with some people who want to stop farming practices that hurt animals. So you make a plan and go to protest these practices. You get there, and wow, the protest is huge. You never expected this, you were just goofing off. Well now everyone who was there is suspect. Even though you technically had the right to protest, you're now considered a dangerous person.
With this tech in place, the government doesn't have to put you in jail. They can do something more sinister. They can just email you a sexy picture you took with a girlfriend. Or they can email you a note saying that they can prove your dad is cheating on his taxes. Or they can threaten to get your dad fired. All you have to do, the email says, is help them catch your friends in the group. You have to report back every week, or you dad might lose his job. So you do. You turn in your friends and even though they try to keep meetings off grid, you're reporting on them to protect your dad....
Maybe Obama won't do it. Maybe the next guy won't, or the one after him. Maybe this story isn't about you. Maybe it happens 10 or 20 years from now, when a big war is happening, or after another big attack. Maybe it's about your daughter or your son. We just don't know yet. But what we do know is that right now, in this moment we have a choice. Are we okay with this, or not? Do we want this power to exist, or not?
I actually get really upset when people say "I don't have anything to hide. Let them read everything." People saying that have no idea what they are bringing down on their own heads. They are naive, and we need to listen to people in other countries who are clearly telling us that this is a horrible horrible sign and it is time to stand up and say no.
2013/6/7
Recently leaked slides from a NSA PowerPoint presentation have revealed that US internet companies, including Google, Facebook, Microsoft and Apple have been giving the NSA access to their users' private data since 2007. The data in question includes emails, instant messages, video and voice chat, stored data, online social networking details and “special requests”. The programme for harvesting this data is known internally as PRISM. This revelation comes a day after revelations that the NSA is indiscriminately collecting phone records of US mobile phone company customers, including their locations and whom they have been calling/texting and when.
The companies implicated in the slide deck have issued carefully-worded denials, claiming that they have never heard of anything called PRISM (likely, as that was probably an internal NSA codename not revealed to the outside world), have never provided the NSA with direct access to their servers (which could just mean that the NSA had to request items of data, or sets of items of data, and got an itemised bill for them).
Of course, this would mean that the NSA has had the task of wading through vast amounts of trivia: of social chatter, chain letters, forwarded amusing cat/sloth/lemur photos (which they'd have to check for steganographed terrorist plans, of course), mundane updates about people's lunch choices/music listening/reaction to last night's Game Of Thrones episode, online shopping receipts, steamy texts to lovers, drunkfaced party photos, viral ads, skinnerbox game invitations, complaints about traffic/public transport/coworkers and such. Though one wonders to what extent this can be automated. For decades, the US intelligence community has been investing millions in artificial intelligence research (a holy grail of CIA-funded research a while ago was the problem of “gisting”, or accurately summarising large amounts of text for human consumption; this is a hard problem, because it requires semantic knowledge about what the text is about). Meanwhile, in the private sector, data mining has shown uncannily accurate results, to the point where retailers have to insert a few deliberately inaccurate or useless coupons into the books they send to customers as not to freak them out with how much they know their true heart. (Remember the story about the angry father demanding why Target was sending his teenage daughter coupons for nappies and prams, and then apologising a few weeks later when she confessed that she was actually pregnant?)
If the NSA has had an firehose-like feed of personal information on millions of individuals for years, it's not unreasonable to expect that some proportion of the multi-trillion-dollar US “black budget” has been allocated to research into finding ways of aggregating, interpreting and processing this information to build up summaries or models of individuals. These could be automated dossiers with estimated personality profiles (“probabilities of paranoia: 23% issues with authority: 17%, narcissism: 27%, procrastination: 53%, adherence to routine: 61%. Most likely to fear: abandonment (41%), cancer (37%), rats (29%), exposure of peccadillos (23%). Probably responsive to: intimidation (43%), flattery (37%)”), which could be useful if the powers that be need to apply subtle, very precise pressure on a conveniently located bystander to use them against someone like al-Qaeda or Occupy. If they have real-time information, such as the mobile phone metadata (and, even omitting the content of conversations, having a record of the location of a person's phone can reveal a lot about what they're doing), they could even get alerts when somebody deviates from their routine more than they typically do; a dive into their private data would reveal whether they're planning a surprise anniversary party for their spouse or a terrorist attack. (Spoiler: it's almost never a terrorist attack.)
Of course, what the social and psychological effects of such surveillance are is another question. If there is a class of watchers, who can peer into the deepest secrets of the rest of the population, would their attitude to the pitiful, flawed wretches before them, with their pathetic little sins and failings, not be one of contempt? Would they not start regarding the rest of the population as little more than cattle, much as the participants in the Stanford Prison Experiment did?
2008/1/13
Details of how the NSA hacked cryptography machines from Swiss company Crypto AG, inserting an undetectable security hole which allowed them to read the traffic of users (including Iranian government orders to assassins and terrorists including the Lockerbie bombers):
On the day of his assassination and one day before his body was found with his throat slit, the Teheran headquarters of the Iranian Intelligence Service, the VEVAK, transmitted a coded message to Iranian diplomatic missions in London, Paris, Bonn and Geneva. "Is Bakhtiar dead?" the message asked.
"Different countries need different levels of security. The United States and other leading Western countries required completely secure communications. Such security would not be appropriate for the Third World countries that were Crypto's customers," Boris Hagelin explained to the baffled engineer. "We have to do it."
Juerg Spoerndli left Crypto AG in 1994. He helped design the machines in the late '70s. "I was ordered to change algorithms under mysterious circumstances" to weaker machines," says Spoerndli who concluded that NSA was ordering the design change through German intermediaries.
The ownership of Crypto AG has been to a company in Liechtenstein, and from there back to a trust company in Munich. Crypto AG has been described as the secret daughter of Siemens but many believe that the real owner is the German government.
2002/6/6
Loose Talk Is Noose Talk: A look at the NSA's retro-styled information-security posters. Very retro, and not too unlike Soviet Socialist Realism.
Tangent #1: Does anybody remember the old Microsoft Word for Windows installer, from the days when it came on floppies and ran on Windows 3.1? It had the usual set of images shown whilst installing, but to save space, they were all vector images, of neat arrays of documents, office computers and such. It struck me how they looked like the late-capitalist equivalent of Soviet propaganda posters.
Tangent #2: Does anybody know where I could find images of the propaganda posters from Terry Gilliam's Brazil?
2001/3/10
2000/7/27
Don't miss: A detailed article, by Duncan Campbell, on the NSA/GCHQ's signals intelligence operations and capabilities, from World War 2 to Echelon.
Entering Chicksands' Building 600 through double security fences and a turnstile where green and purple clearance badges were checked, the visitor would first encounter a sigint in-joke - a copy of the International Telecommunications Convention pasted up on the wall. Article 22 of the Convention, which both the United Kingdom and the United States have ratified, promises that member states "agree to take all possible measures, compatible with the system of telecommunication used, with a view to ensuring the secrecy of international correspondence".
In 1996, shortly after "Secret Power" was published, a New Zealand TV station obtained images of the inside of the station's operations centre. The pictures were obtained clandestinely by filming through partially curtained windows at night. The TV reporter was able to film close-ups of technical manuals held in the control centre. These were Intelsat technical manuals, providing confirmation that the station targeted these satellites. Strikingly, the station was seen to be virtually empty, operating fully automatically.
Key word spotting in the vast volumes of intercepted daily written communications - telex, e-mail, and data - is a routine task. "Word spotting" in spoken communications is not an effective tool, but individual speaker recognition techniques have been in use for up to 10 years. New methods which have been developed during the 1990s will become available to recognise the "topics" of phone calls, and may allow NSA and its collaborators to automate the processing of the content of telephone messages - a goal that has eluded them for 30 years.
Under the rubric of "information warfare", the sigint agencies also hope to overcome the ever more extensive use of encryption by direct interference with and attacks on targeted computers. These methods remain controversial, but include information stealing viruses, software audio, video, and data bugs, and pre-emptive tampering with software or hardware ("trapdoors").
1999/11/4